8 High-Impact Code Review Tips to Catch Bugs Before They Ship
Boost software security and catch vulnerabilities early with expert source code review services that improve code quality, resilience, and reliability.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
What Is a Security Code Review?
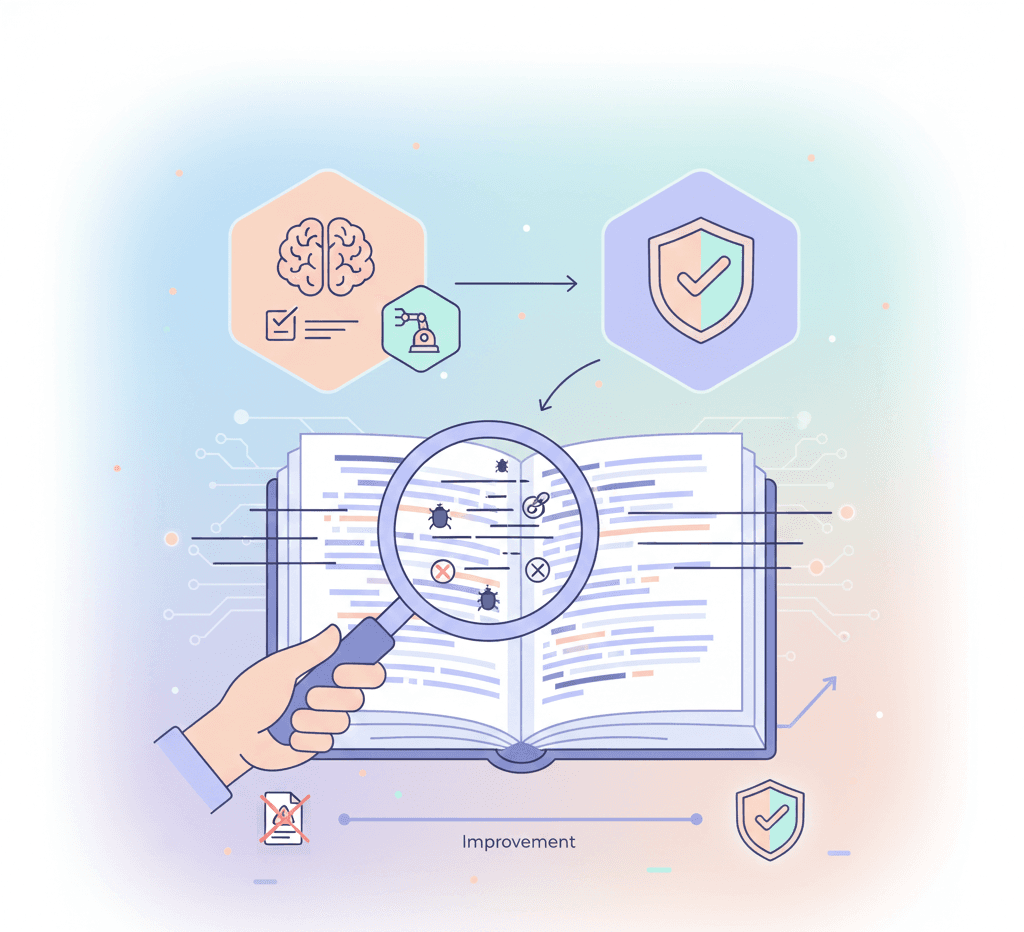
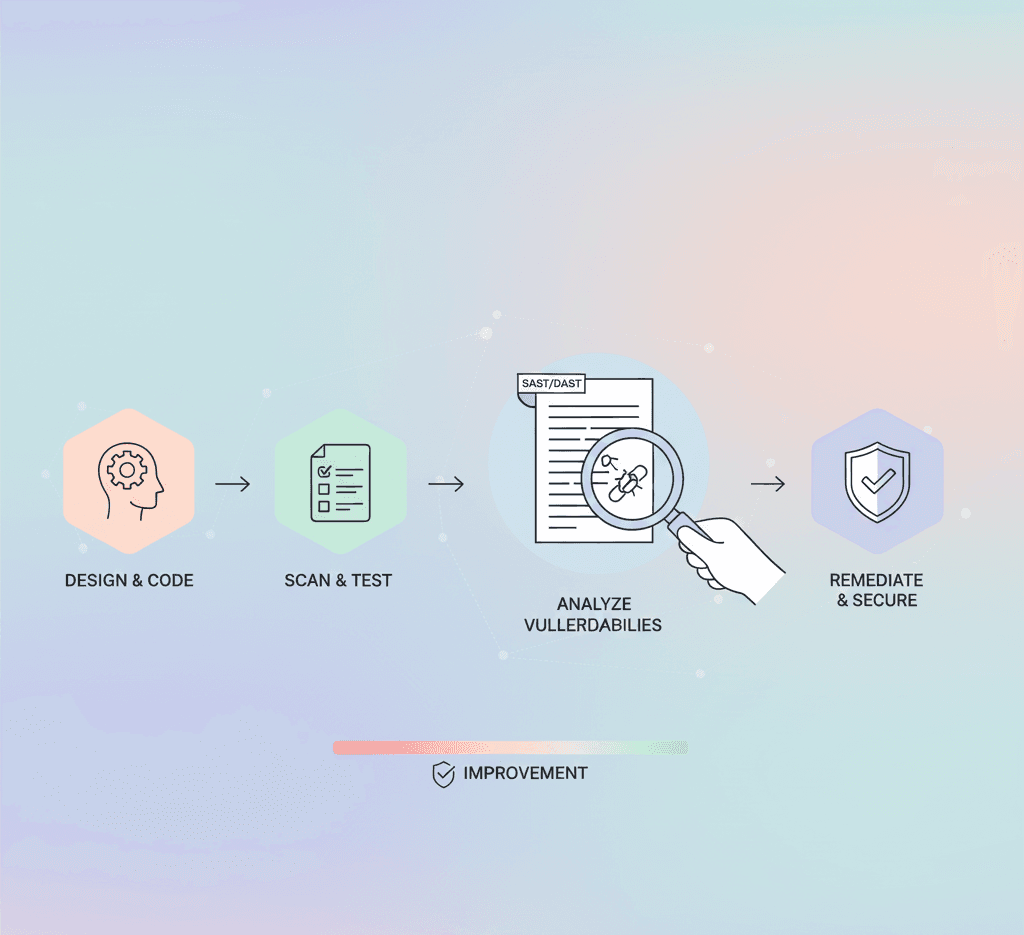
A security code review is the process of inspecting source code to evaluate how well it defends against external threats. It helps uncover security flaws and logical inconsistencies that could compromise an application or its surrounding systems. While automated tools are essential for identifying common vulnerabilities, peer reviews provide the human insight necessary for thorough analysis. Together, these processes enable a comprehensive source code inspection to safeguard your applications.
Implementing source code review services allows organisations to detect and address vulnerabilities early, reducing the risk of data loss, revenue disruption, and reputational harm. By incorporating both automated and manual review techniques, development teams can produce robust, high-quality software and adhere to best practices in source code review in cybersecurity.
Why Peer Reviews Matter
Manual code reviews offer a critical layer of protection that complements automated tools. Developers, despite their expertise, can overlook subtle bugs or vulnerabilities. A peer review process introduces fresh perspectives from team members with diverse skills. This collaborative approach can reveal issues that automated systems or the original developer might miss.
That said, organising an efficient and consistent peer code review can be challenging. To simplify the process and improve results, consider these eight proven code review strategies.
1. Use Comments to Explain Code Intent
Adding meaningful comments while writing code is a powerful way to guide reviewers. These non-functional comments help reviewers understand the purpose behind each block of code. This practice reduces confusion and enables quicker, more effective feedback.
2. Never Assume Code Works Without Testing
Code creation is an iterative process. Developers should continuously test their work to confirm its functionality. Implementing practices like Test-Driven Development (TDD), where unit tests are written before the code itself, helps verify that each block performs its intended function and integrates cleanly within the software development code review process.
3. Run Automated Test Suites Before Review
Automated test suites validate specific procedures by comparing outputs to expected results. They highlight performance issues and functionality errors before the manual review begins. Combined with tools like an xss auditor, these checks can reveal injection or cross-site scripting risks that would otherwise go unnoticed.
4. Keep Pull Requests Small and Focused
Pull requests (PRs) should have a narrow scope to ensure clarity. PRs under 250 lines are ideal, as they allow reviewers to identify 70–90% of defects in less than an hour. Overly broad PRs can lead to missed issues and longer turnaround times.
5. Leverage Automated Code Checkers
Before submitting a PR, developers should use static code analysis tools or linters to catch formatting and structural issues. These tools act like spellcheck for your code, reducing noise in manual reviews and helping ensure injection attack prevention by spotting weak or unsafe query patterns (e.g., the best way to avoid SQL injection is through prepared statements or ORMs).
6. Review All Code and PRs Holistically
Every PR, regardless of size, should be reviewed thoroughly. Even small changes can introduce vulnerabilities or impact other parts of the system. Reviewers must assess the code holistically for cohesion, consistency, and security — including areas vulnerable to attack, such as cybersecurity SQL injection or leaks from poor data handling.
7. Limit Review Duration and Scope
Long review sessions can lead to fatigue and oversight. Studies show that reviewers should not exceed 60 minutes or 400 lines of code per session. Setting clear limits ensures focus and attention to detail.
8. Always Conduct a Security Code Review
A secure code review examines how well the code resists malicious attacks. It focuses on logic flaws, data handling, authentication, and other high-risk areas. This is crucial for source code review in cyber security, as vulnerabilities like SQL injection or XSS can be exploited quickly and widely.
Security Checklist:
Use SAST tools like Snyk Code for early detection of vulnerabilities.
Apply secure coding standards (e.g., OWASP Top 10).
Limit access to sensitive code sections.
Check for unvalidated inputs (learn via an SQL injection attack demo).
Implement Secrets Management to protect credentials.
Include cross-browser checks or forms tests, such as manual Selenium testing, where appropriate.
Secure code review services can significantly improve your application’s resilience by uncovering weaknesses that lead to data breaches or intellectual property loss — and can provide a secure code review report that highlights weaknesses and offers remediation steps.
Final Takeaway: How to Do a Code Review the Right Way
No matter how experienced the developer, no single person can catch every issue. That’s why a multi-layered code review process is vital. Combining automated code checks, peer reviews, and secure code inspection provides the most complete picture of your software’s health.
By following these eight strategies, your development team can build more secure, maintainable, and high-quality code. Whether you're leveraging internal reviewers or professional source code review services, integrating these best practices into your workflow ensures your applications are reliable — and ready to withstand modern cyber threats.