Review Smarter: A Tactical Guide to Secure Code Analysis
Improve software security with expert insights from a secure code review report, helping teams identify risks, fix vulnerabilities, and build safer applications.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
We’ve all experienced it—staring at lines of code, wondering if there’s a security flaw quietly waiting to cause chaos. That’s where secure code reviews come in. Think of them as your final defence against bugs and vulnerabilities that could compromise your entire application.
Here’s a sobering truth: even advanced AI models like LLMs suggest insecure code around 30% of the time. So, while automation helps, nothing replaces a sharp, experienced eye during the review process.
In this guide, you’ll learn how to perform a secure code review from start to finish—so you can lock down your software before threats become real.
What Is a Secure Code Review—and Why Does It Matter?
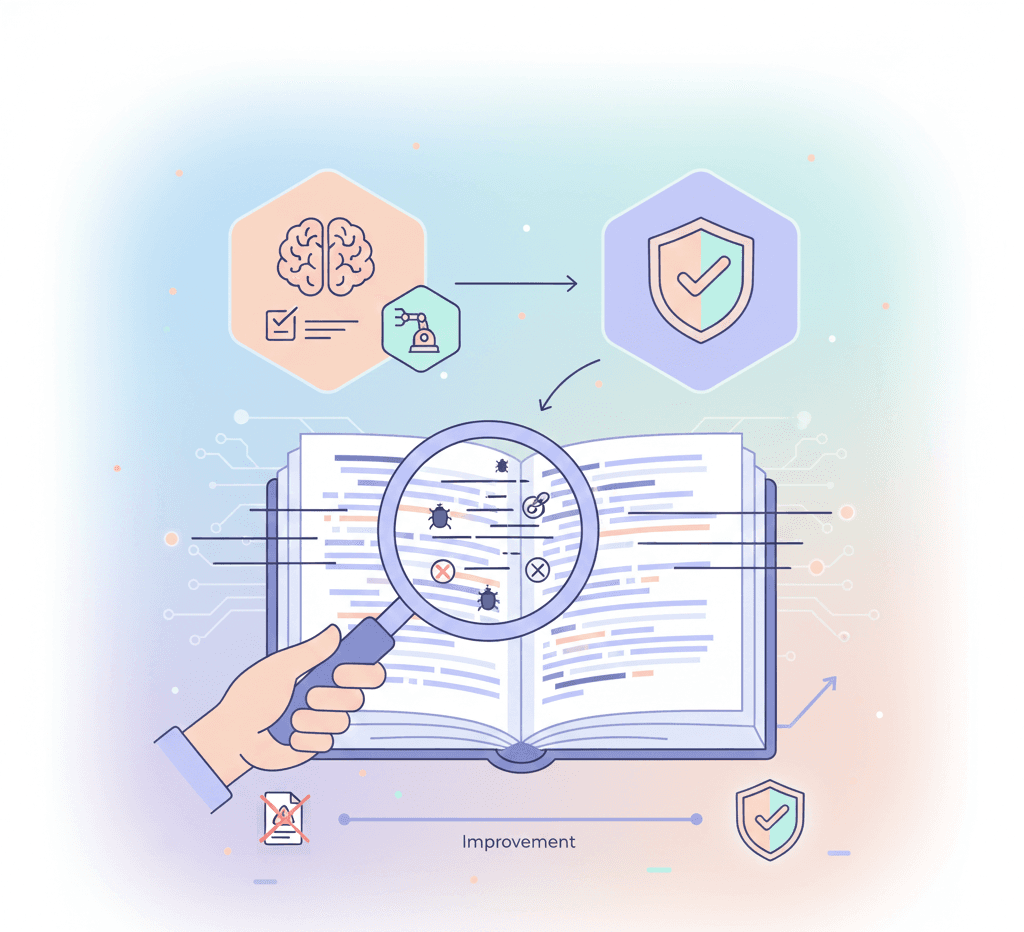
A secure code review is a systematic examination of source code to identify security flaws, risky logic, and non-compliance with secure coding standards. It’s not just about catching bugs—it's about ensuring your application is resistant to exploitation.
Why You Should Care:
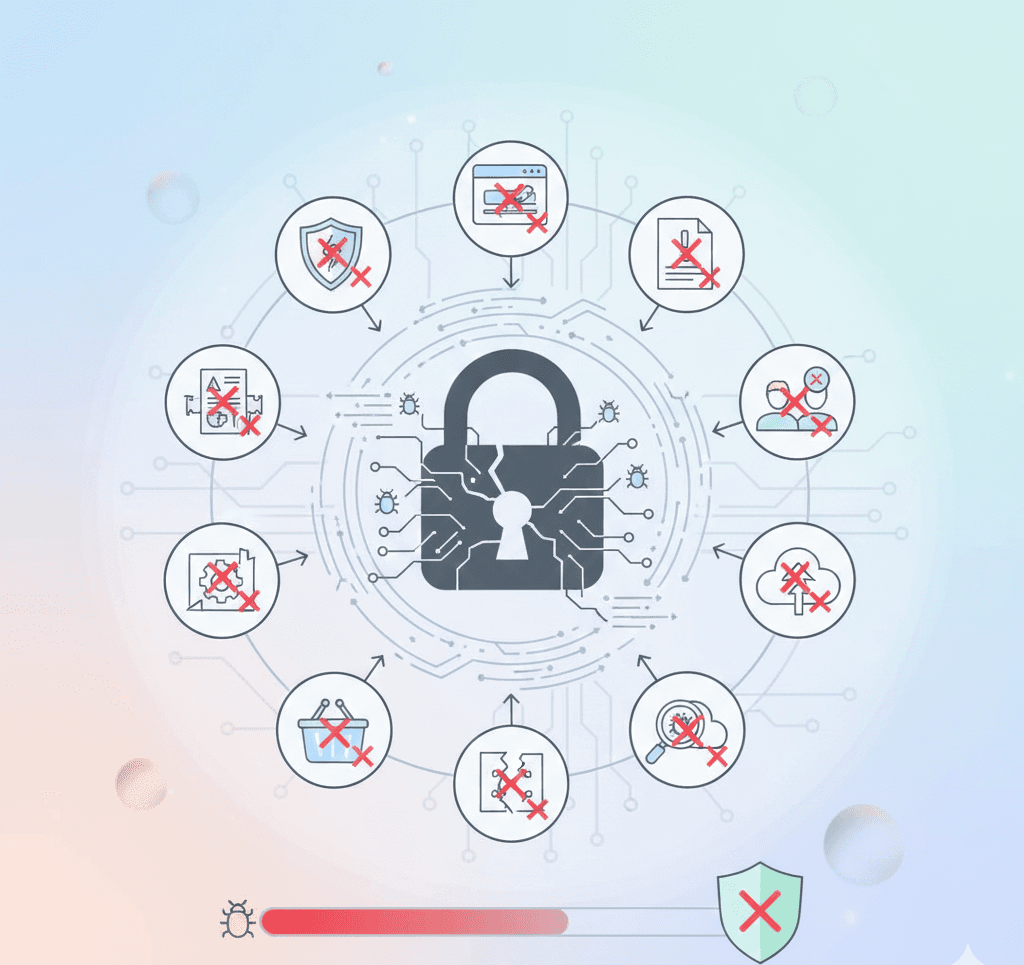
Every line of code is a potential attack surface.
Common issues like SQL injection, XSS, and buffer overflows usually trace back to small oversights.
Secure code reviews reduce risk and promote better development practices.
Beyond catching vulnerabilities, secure reviews improve overall code quality, encourage collaboration, and build a security-first mindset across your team. Effective source code review in cyber security ensures your application isn't just functional, but fortified.
Preparing for a Secure Code Review
A successful review starts well before the first line of code is examined. Here's how to prepare:
1. Use the Right Tools
Start with automated scanning tools that catch common vulnerabilities early:
Static analysis tools like SonarQube or Semgrep
Secrets detection with Git Secrets
Dependency checkers like Snyk or OWASP Dependency-Check
Automation forms the backbone of the smart software development code review process, but it doesn’t replace expert human intuition.
2. Secure the Review Environment
Code under review might contain sensitive logic or data. Follow these steps:
Limit access to reviewers only
Use isolated environments
Apply DevSecOps principles to integrate security into CI/CD pipelines
3. Establish Review Guidelines & Checklists
Use tailored checklists to maintain consistency across source code inspection. Your checklist should include:
Input validation and output encoding
Authentication and session management
Encryption and proper storage of sensitive data
Error handling and logging
Checklists ensure no stone is left unturned—even for complex issues like injection attack prevention or advanced scenarios such as understanding the best way to avoid SQL injection.
4. Align Your Team
Set expectations early by clarifying:
Review goals
Assigned roles
High-risk areas (such as payment gateways or third-party APIs)
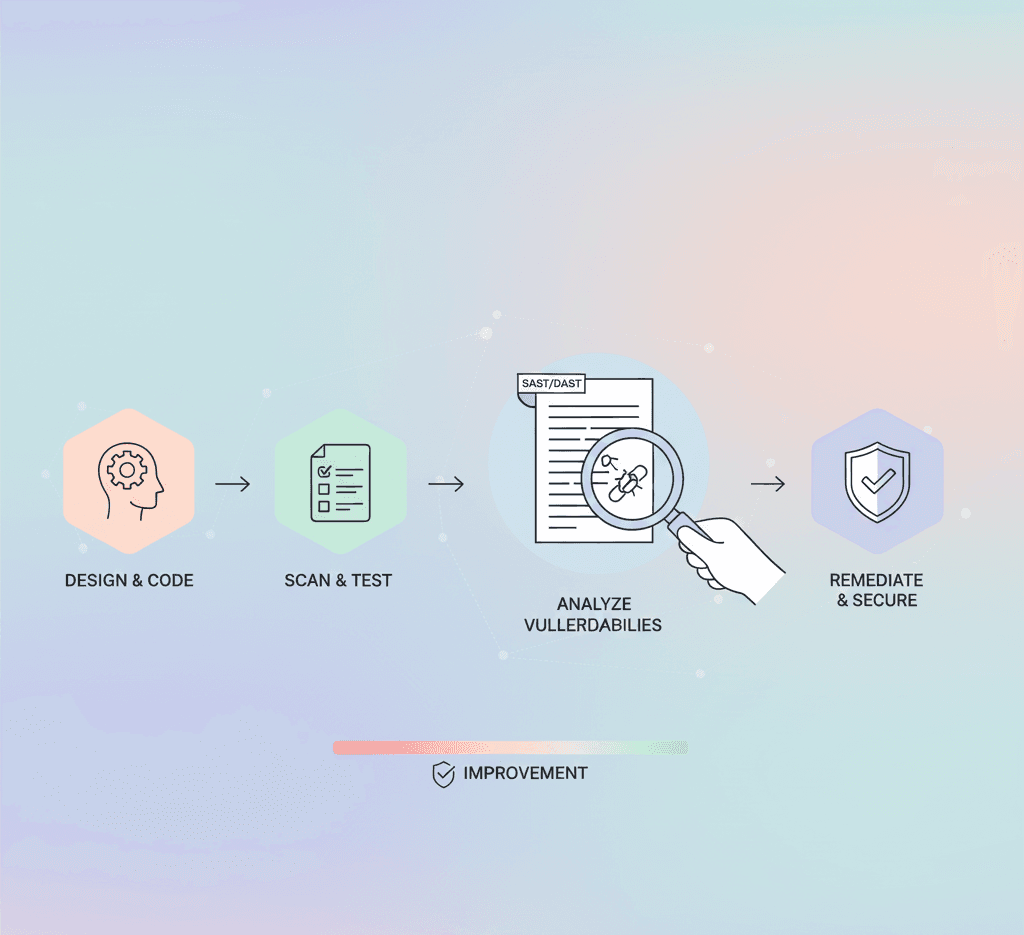
The Secure Code Review Process (Step-by-Step)
Once preparation is complete, follow this structured process to maximise effectiveness:
Step 1: Initial Assessment
Understand the codebase before reviewing:
Read documentation: Study architecture and flows
Identify high-risk areas: Code handling user input or sensitive logical workflows
Determine risk levels: Focus on parts where a cyber security SQL injection breach would be catastrophic
Step 2: Run Static Code Analysis
Use automated tools to perform an initial scan:
Scan for insecure functions and code smells
Prioritise findings by severity
Use results to guide manual review—don’t rely on them exclusively
Step 3: Perform Manual Review
This is where skilled professionals shine. Look for:
Weak or missing input validation
Hardcoded credentials
Insecure session and auth implementations
Logic errors that bypass the intended workflow
This is also where tools like an XSS auditor or specialised source code review services may flag high-risk flaws like cross-site scripting or logic bypass attacks.
Step 4: Review Third-Party Libraries and Dependencies
Dependencies are a common point of exploitation:
Scan using npm audit, yarn audit, or Snyk
Check for CVEs and bad maintenance practices
Sandbox or replace outdated or risky libraries
Step 5: Testing and Validation
Validate your findings:
Run unit and integration tests
Simulate real-life threats (e.g., SQL injection attack demo)
Use techniques like fuzzing and manual selenium testing for end-to-end validation
After the Code Review: What Comes Next?
Post-review activities help boost long-term resilience:
Communicate findings with actionable reports (like a secure code review report)
Track and validate remediation
Train teams based on common weaknesses
Ongoing Best Practices for Secure Code Reviews
Security is not a one-time milestone. Maintain momentum by:
Scheduling regular reviews
Updating checklists and logic based on evolving threats
Celebrating developers who advocate for secure coding practices
Automating recurring tasks in your CI pipeline
Final Thoughts: Build Security into Every Line of Code
Performing a secure code review isn’t just about avoiding risk—it’s about building trust, stability, and resilience into your application.
By combining the right tools, processes, and mindset, your team can confidently release secure software—even in a rapidly evolving threat landscape.
From injection attack prevention to mastering the software development code review process, it’s clear: secure code is smart code.