What is Source Code Review: A Comprehensive Guide 2025
Enhance application security with expert source code review services that uncover vulnerabilities, strengthen code quality, and support compliance.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
In today's digital-first world, your software is your fortress—and the code is the foundation. But even the strongest foundation can crack if it’s not properly examined. That’s where source code review in cyber security comes in. It’s not just a technical formality; it’s a strategic layer of protection for your applications, your users, and your business.
At Accorp, we treat source code inspection like detective work—digging deep, exposing hidden vulnerabilities, and delivering real value with actionable insights.
In this comprehensive guide, we’ll explore what source code review is, why it’s vital for application security, the difference between general and secure code review, and how your business can benefit from a professionally executed secure code review report and other source code review services.
What Is Source Code Review in Cyber Security?
Source code review is the process of examining an application’s codebase to identify bugs, vulnerabilities, and design flaws that could be exploited by attackers. It can be automated, manual, or ideally—a combination of both. Unlike black-box testing (where the code isn’t visible to testers), source code review gives full visibility into the application’s logic, workflows, and security controls. This allows for a more thorough security analysis, catching flaws that are hard to detect through surface-level testing.
(As part of a robust software development code review process, teams often combine automated scans with human-led reviews to catch both pattern-based issues and subtle logic flaws.)
Source Code Review vs Secure Code Review: What’s the Difference?
While often used interchangeably, source code review and secure code review serve slightly different purposes:
Source Code Review
Focuses on detecting bugs, performance issues, and logic errors
Ensures adherence to coding standards and team guidelines
Typically part of the regular development process
Secure Code Review
Specifically targets security vulnerabilities like SQL injection, XSS, insecure authentication, etc.
Prioritises threats that can lead to data breaches or compliance issues
Usually performed by cybersecurity experts with specialised tools (for example, an XSS auditor or tools used for cyber security SQL injection testing)
At Accorp, we go beyond standard code reviews. Our experts conduct secure code inspections that dig into the security posture of your applications, helping you build software that’s not just functional, but fortified.
Why Is Source Code Inspection Important?
With over 3.48 million apps on the Google Play Store and nearly 4,000 new apps launched daily, cybersecurity threats are more prevalent than ever. A single overlooked vulnerability can lead to devastating outcomes—data breaches, service disruptions, or worse, reputational damage.
Here’s why source code inspection should be a cornerstone of your SDLC:
Early Detection: Fix vulnerabilities before they reach production
Decreased Costs: Catching issues early means fewer hotfixes later
Improved Quality: Clean, secure code is easier to maintain and scale
Regulatory Compliance: Helps meet standards like GDPR, HIPAA, PCI-DSS
Benefits of a Secure Code Review Report
At Accorp, our reports offer deep insights, root cause analysis, remediation recommendations, and risk assessments that empower developers to act with confidence. Here are the top benefits:
Identify Bugs and Vulnerabilities
Pinpoint logic flaws, insecure APIs, and unhandled exceptions—before attackers do.Facilitate Knowledge Sharing
Code reviews help team members learn best practices and share expertise across the board.Enforce Compliance and Coding Standards
Ensure your application adheres to security benchmarks and regulatory requirements.Accelerate Development
Early fixes save time during testing and deployment phases.Strengthen Documentation and Reporting
Track vulnerabilities, decisions, and remediations in a structured, easy-to-understand report.
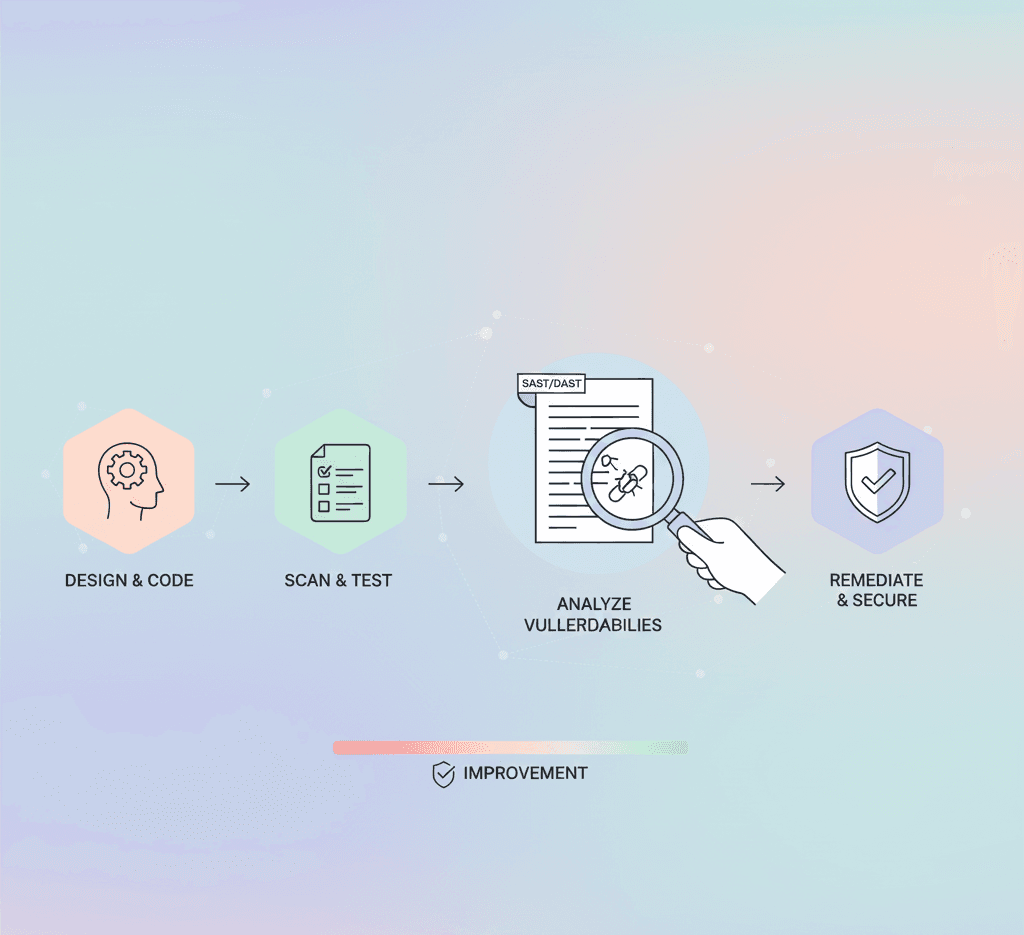
How Accorp Performs Source Code Review
We use a hybrid model that combines automated tools with manual testing by cybersecurity experts. This eliminates false positives and ensures comprehensive coverage.
Automated Tools (SAST)
Scan code during development
Identify security patterns and known issues
Flag concerns across third-party libraries
Manual Inspection
Performed by senior security analysts
Detects logic flaws, business-specific risks, and complex vulnerabilities
Prioritises real-world risk context
Reporting & Remediation Support
Receive a detailed, prioritised secure code review report
Includes vulnerability classifications (CVSS scores), line-by-line references, and remediation steps
Optional retesting after fixes to verify effectiveness
(We also include checks for common web issues—an XSS auditor step to spot cross-site scripting risks and targeted tests for injection attack prevention techniques.)
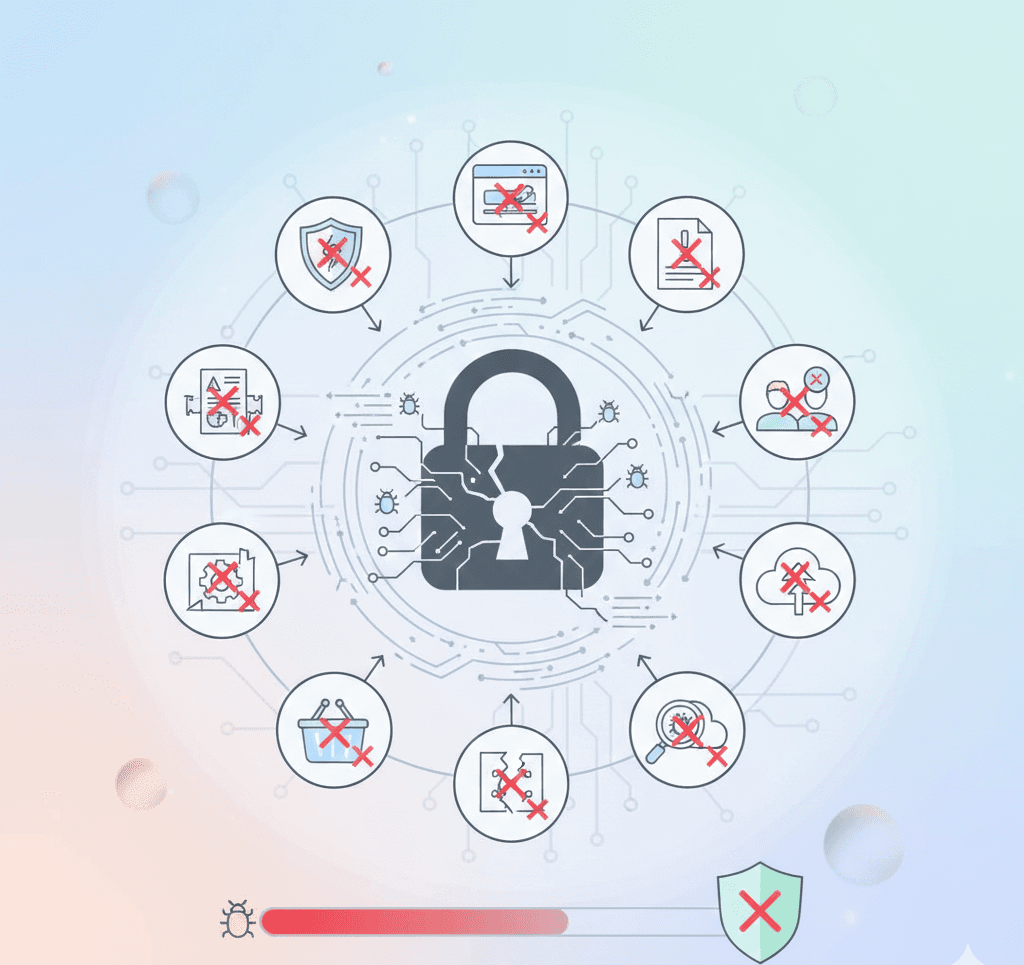
Challenges in Source Code Review
Even with expert tools and techniques, challenges remain. Here are some common pitfalls we help clients overcome:
Poor Input Validation Leads to injection flaws like SQLi or XSS. Every input must be sanitised.
Weak Authentication & Authorisation — Poor session management or hardcoded credentials open serious attack vectors.
Inadequate Logging — If incidents can’t be traced, response and forensics become impossible.
Insecure Configurations — Misconfigured settings leave sensitive endpoints exposed.
Improper Error Handling — Revealing stack traces or database errors gives hackers insight.
(We demonstrate cybersecurity SQL injection risks via controlled examples and provide actionable guidance on injection attack prevention.)
Best Practices for Effective Source Code Review
Our approach to source code review in cyber security is guided by these proven best practices:
Define Clear Security Goals — Tailor reviews to your business logic and threat model.
Protect Sensitive Data — Use secure cryptography and strong encryption algorithms.
Implement Strong Authentication — Enforce MFA and secure password policies.
Stay Informed on Threats — Our analysts stay updated with the latest CVEs and OWASP Top 10.
Use Advanced Tools — Static analysers, linters, and custom rule sets improve coverage.
Why Choose Accorp for Source Code Review?
At Accorp, we don’t just find issues—we help you build better, more secure software. Our experienced cybersecurity professionals deliver precision-based reviews backed by real-world attack scenarios and development insight.
Zero False Positives
Detailed, Developer-Friendly Reports
Manual & Automated Hybrid Audits
Fast Turnaround & Retesting Support
When it comes to source code review in cyber security, trust Accorp to deliver thorough, expert-driven insights that protect your application and elevate your development process.