The Code Review Trap List: 10 Mistakes You Can’t Afford to Make
Avoid common mistakes in source code review in cyber security and strengthen software by identifying risks, fixing flaws, and improving code quality.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
Are you making these costly mistakes in your source code reviews? At Accorp, we understand that an effective source code inspection is vital to uncovering hidden vulnerabilities that can compromise your software’s integrity and security. In this guide, we expose the top 10 common mistakes developers and security teams make during code reviews—and how you can avoid them to deliver robust, high-quality software.
Whether you're conducting an internal audit or partnering with source code review services, avoiding these pitfalls is key to producing a trustworthy and secure application.
What Is Source Code Review?
Source code review is a systematic examination of an application's codebase to identify bugs, logic errors, security flaws, and non-compliance with best practices. This process is essential in source code review in cyber security and quality assurance, helping developers spot issues that automated tools might miss.
By using structured source code inspection techniques and generating a secure code review report, organisations can greatly improve the resilience of their software and reduce the attack surface.
Why It Matters
Studies show that code reviews can catch up to 90% of software defects. In fact, IBM research revealed that manual reviews found an average of 63 defects per 1,000 lines of code, compared to just 12 with unit testing alone. That’s a massive difference that highlights the need for well-executed code reviews.
Top 10 Mistakes in Source Code Review (and How to Fix Them)
1. Lack of Input Validation
Failing to validate user input can open the door to attacks like SQL injection, XSS, and buffer overflows. A recent study showed that over 40% of web applications contain input validation vulnerabilities.
Best Practices:
Use whitelisting and regular expressions for input sanitisation.
Employ parameterised queries — the best way to avoid SQL injection is to avoid string-concatenated queries.
Escape and sanitise all user-generated output before rendering.
Include training with an xss auditor in your testing toolkit to catch cross-site scripting issues early.
(For hands-on training, teams sometimes work through a controlled sql injection attack demo to understand exploitability and prevention.)
2. Improper Error Handling
When systems expose too much information through error messages, attackers can exploit those details to gain access.
Best Practices:
Suppress detailed errors from users; log them internally.
Avoid exposing system paths, server versions, or stack traces.
Use secure logging frameworks.
3. Insecure Cryptographic Storage
Using outdated or weak cryptographic practices endangers sensitive data such as passwords and API keys.
Best Practices:
Use industry-standard algorithms (e.g., AES, RSA).
Secure key management and key rotation policies.
Avoid deprecated or homegrown encryption.
4. Insecure Communication Channels
Transmitting sensitive data over insecure protocols like HTTP or outdated SSL versions exposes users to interception and man-in-the-middle attacks.
Best Practices:
Use TLS 1.2+ and enforce HTTPS everywhere.
Disable insecure protocols like SSLv3.
Validate certificates and use secure cyphers.
5. Weak Authentication and Authorisation
Improper implementation of access control can lead to privilege escalation and unauthorised access.
Best Practices:
Enforce MFA (multi-factor authentication).
Store passwords securely (bcrypt, scrypt).
Regularly audit and update access controls.
6. Insufficient Logging and Monitoring
Without proper visibility, attacks can go undetected for months.
Best Practices:
Log security-relevant events (logins, failures, privilege changes).
Monitor logs in real-time using SIEM tools.
Set alerts for suspicious behaviour.
7. Misconfigured Security Settings
Configuration files and server settings often harbour silent vulnerabilities.
Best Practices:
Review and lock down configuration files.
Disable unused ports and services.
Perform regular config audits using automated tools.
8. Poor Software Design
Security starts with architecture. If the design is flawed, code-level fixes can’t compensate.
Best Practices:
Follow secure design principles (least privilege, defence-in-depth).
Conduct threat modelling during planning.
Use secure architecture patterns.
9. Insecure Deployment Processes
A secure codebase can still be compromised during deployment if DevOps practices are not secure.
Best Practices:
Secure CI/CD pipelines with proper authentication and access control.
Validate third-party components.
Store credentials (e.g., API keys) securely using vault tools.
Integrate manual selenium testing and automated checks into the software development code review process to ensure deployment-time issues are caught.
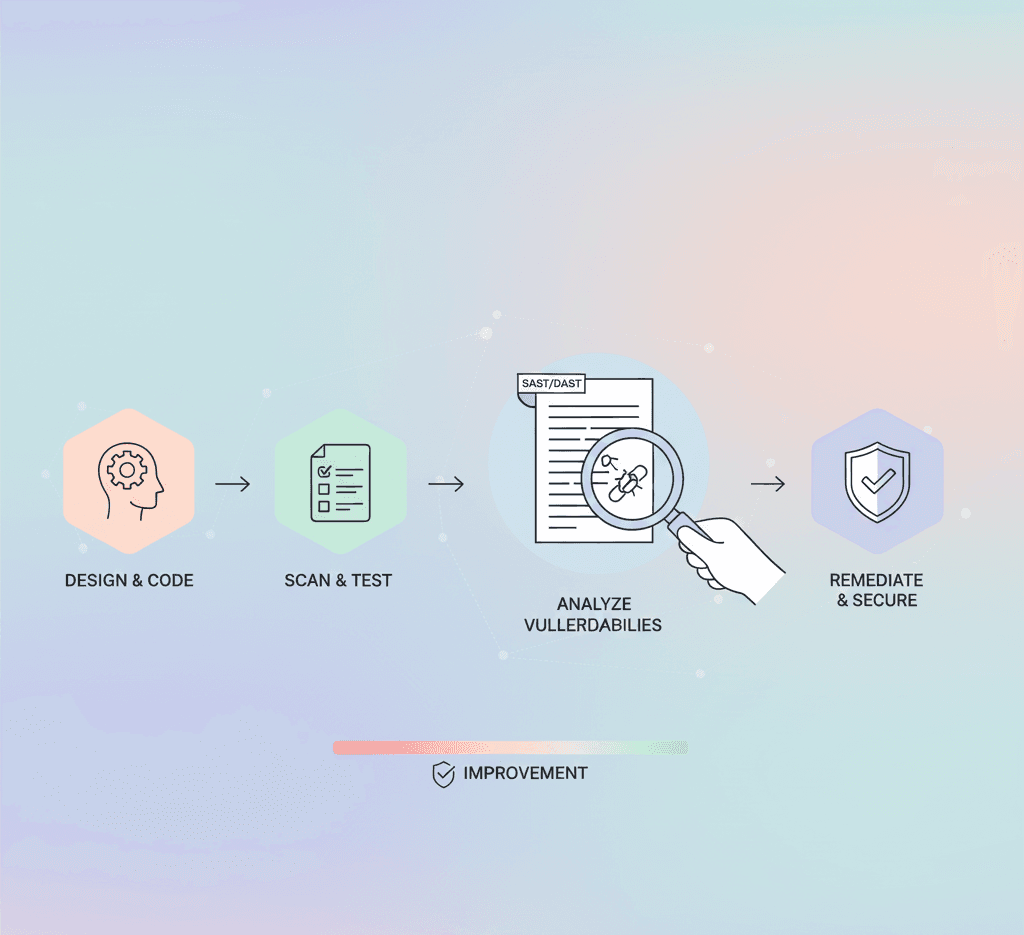
10. Inadequate Security Testing
If you're only testing for functionality, you're missing the bigger picture.
Best Practices:
Use automated static and dynamic analysis tools.
Perform regular vulnerability scans and vulnerability and penetration testing.
Integrate security into your CI/CD pipeline.
Final Thoughts: Secure Code Review Is a Must-Have
A well-executed source code review in cyber security is not just a best practice—it's a business-critical function. By avoiding these 10 mistakes and leveraging professional source code review services, you can significantly reduce risk and protect your users and systems.
At Accorp, our expert team delivers comprehensive source code inspection and produces detailed secure code review reports that go beyond surface-level issues. With deep expertise in injection attack prevention, cyber security SQL injection mitigation, and practical demos like sql injection attack demo, we help you build resilient, trusted software.
Whether you’re refining your software development code review process, using an xss auditor, or combining automated tools with manual selenium testing, the right mix of people, process, and tools makes all the difference.