FedRAMP Audit & Certification: A Roadmap to Cloud Compliance Success
FedRAMP Audit & Certification: Your roadmap to cloud compliance success. Learn key steps, scanning phases, and best practices for a smooth FedRAMP assessment.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
Achieving FedRAMP cloud certification is a complex journey—and one of its most demanding components is vulnerability scanning. For Cloud Service Providers (CSPs), aligning with FedRAMP security compliance standards means building a rigorous vulnerability management strategy that’s audit-ready, continuously monitored, and transparently documented.
This guide walks you through the essential stages of the vulnerability scanning process, offers best practices, and pinpoints common pitfalls that can delay or derail your FedRAMP assessment. Whether you're just getting started or heading into your final scans, this resource will help you stay on track for a successful FedRAMP audit.
What Is FedRAMP Vulnerability Scanning?
FedRAMP vulnerability scanning is a required activity that evaluates your cloud environment's ability to detect, prioritise, and remediate security weaknesses. These scans form a core component of both the FedRAMP readiness assessment and ongoing security monitoring under the FedRAMP system security plan (SSP).
To pass the FedRAMP assessment, your scans must:
Cover your entire system boundary (infrastructure, containers, web apps, databases)
Be authenticated using privileged credentials
Show timely remediation of moderate- and high-risk findings
Be fully documented, including false positives, risk adjustments (RAs), and operational requirements (ORs)
Failing to meet these scanning expectations can lead to significant delays—or even denial of FedRAMP cloud certification.
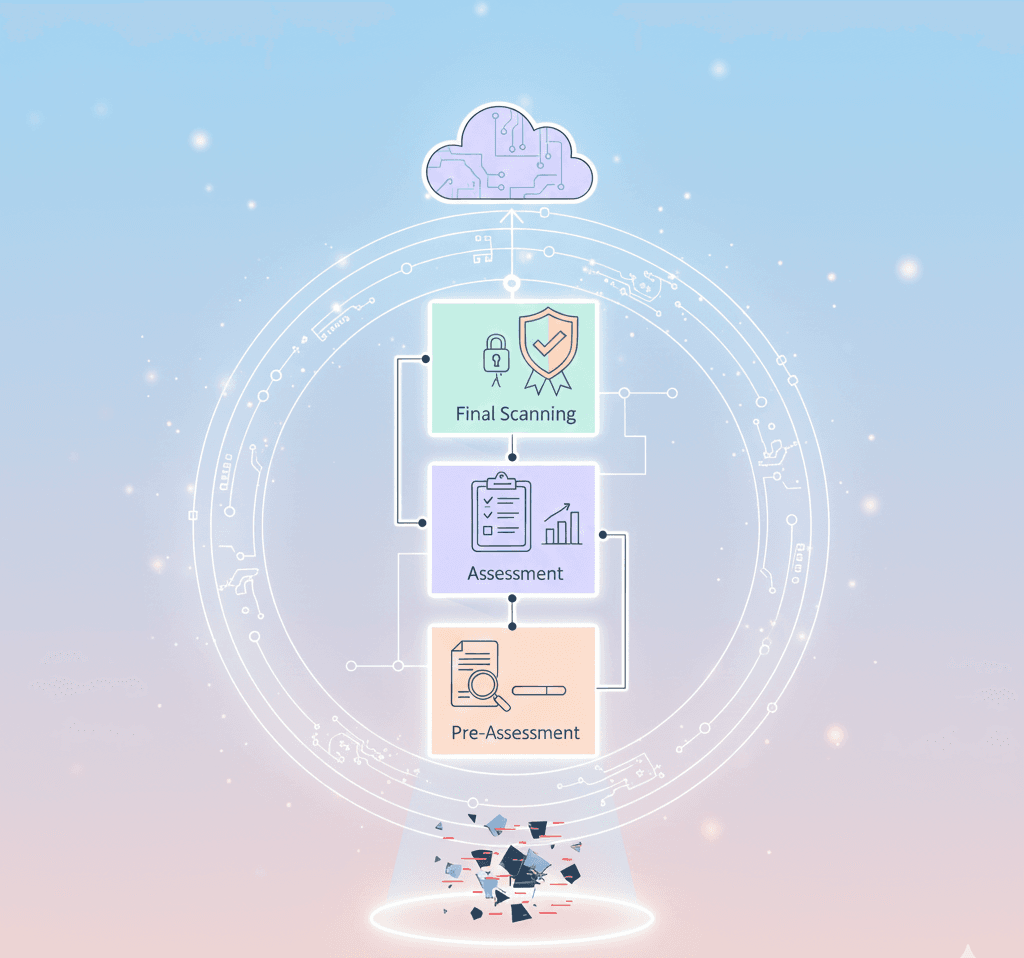
The 3 Phases of FedRAMP Vulnerability Scanning
CSPs pursuing FedRAMP security compliance must complete their vulnerability scanning in three strategic phases:
1. Pre-Assessment Phase
Start this phase 60–90 days before your official FedRAMP readiness assessment. During this stage, CSPs submit recent vulnerability scan results to a certified 3PAO.
Key focus areas:
Ensure scans are authenticated with appropriate credentials
Include all necessary components (cloud infrastructure, VMs, apps, databases)
Enable all relevant plugins and checks
Start mapping false positives (FPs), risk adjustments (RAs), and exceptions
Avoid common pitfalls:
Unauthenticated scans that miss critical vulnerabilities
Partial coverage, such as skipped components
Failing to meet remediation windows (30 days for high, 90 days for moderate findings)
2. Assessment Phase
This phase supports your 3PAO’s creation of the FedRAMP Security Assessment Plan (SAP) and ultimately your FedRAMP Security Assessment Report (SAR). 3PAOs validate your controls, remediation strategies, and documentation accuracy.
Core review areas:
Any changes to tools, configurations, or personnel since pre-assessment
Accuracy and tracking of vulnerabilities in the Plan of Actions & Milestones (POA&M)
Consistent, authenticated scan methodologies
3. Final Scanning Phase
About 30 days before your FedRAMP SAR is finalised, you’ll submit final scans that reflect remediated vulnerabilities and establish readiness for FedRAMP AO (Authorising Official) approval.
Final submission goals:
All high-severity findings should be resolved
Updated POA&M must include all current exceptions, false positives, and risks
Scans should be fully authenticated and cover the full boundary
Best Practices for a Seamless FedRAMP Audit
To ensure a smooth certification process, follow these key strategies:
Automate scans and integrate them into your CI/CD pipeline
Assign clear ownership for scan configs and remediation tasks
Schedule scans to align with the ConMon (continuous monitoring) cadence
Document everything—especially exceptions, deviations, and false positives
Review FedRAMP SSP templates regularly for accuracy and completeness
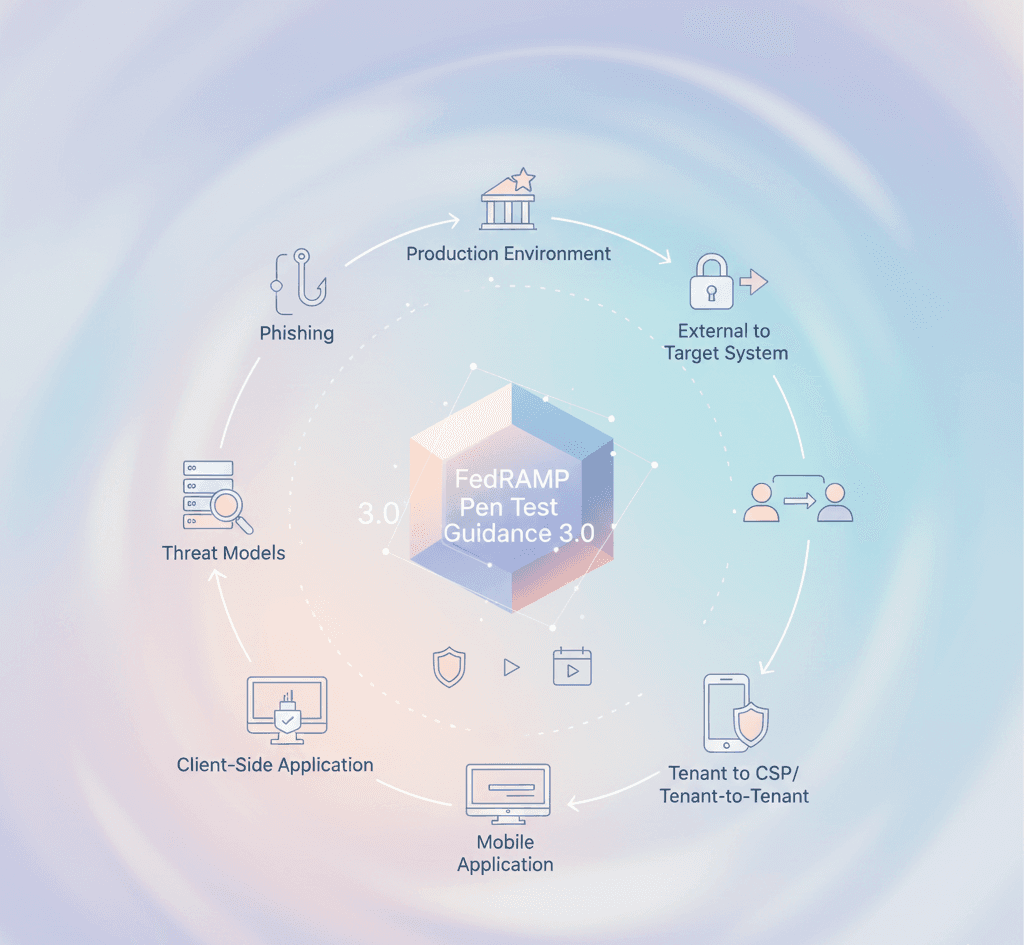
Common Pitfalls That Can Derail Your FedRAMP Cloud Certification
Avoid these frequent FedRAMP mis-steps:
Submitting incomplete or unauthenticated scans
Failing to support false positives and risk exceptions with documentation
Switching scanning tools mid-assessment
Missing shared infrastructure in multi-cloud or SaaS models
Delaying final submissions for the FedRAMP JAB P-ATO pathway or agency review
How Accorp Helps CSPs Prepare for FedRAMP Certification
At Accorp, we guide Cloud Service Providers through every phase of the FedRAMP readiness assessment and certification process. Our services include:
Support with FedRAMP SSP templates and documentation
Hands-on support for FedRAMP SAP and SAR preparation
Secure source code review and vulnerability analysis
Full lifecycle vulnerability scanning and ConMon planning
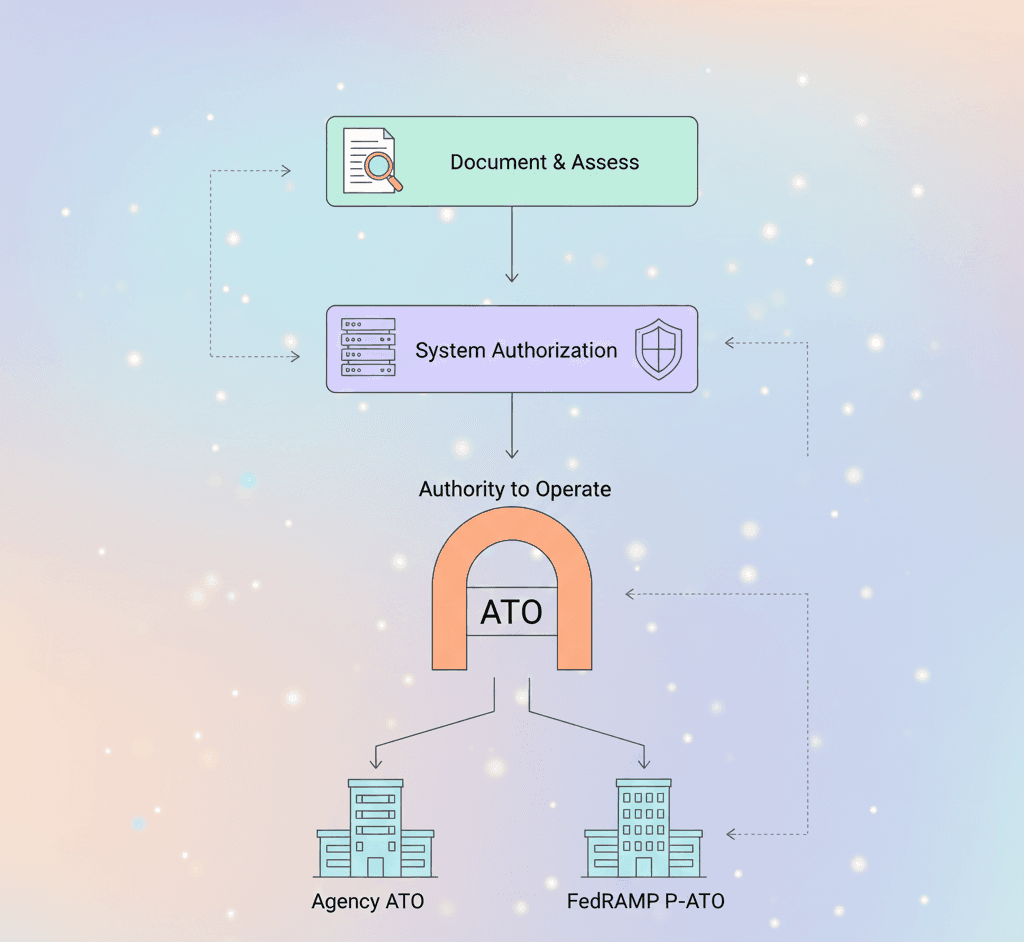
Assistance with both agency ATO and FedRAMP JAB authorisation paths
Whether you’re aiming for your first FedRAMP ATO or maintaining an existing one, we help ensure every requirement is met on time and with confidence.
Final Thoughts: Stay Ahead with Proactive Scanning
FedRAMP security compliance isn’t a one-time achievement—it’s a continuous commitment to federal data protection. A mature vulnerability scanning program, backed by automation and solid documentation, not only safeguards federal workloads but keeps your CSP in good standing for future audits.
With the right approach—and expert support—your path to FedRAMP cloud certification can be streamlined, strategic, and set up for long-term success.