FedRAMP-Compliant Vulnerability Scanning: From Planning to Pitfall Prevention
Master FedRAMP-compliant vulnerability scanning from planning to audit readiness. Avoid pitfalls and strengthen FedRAMP security compliance.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
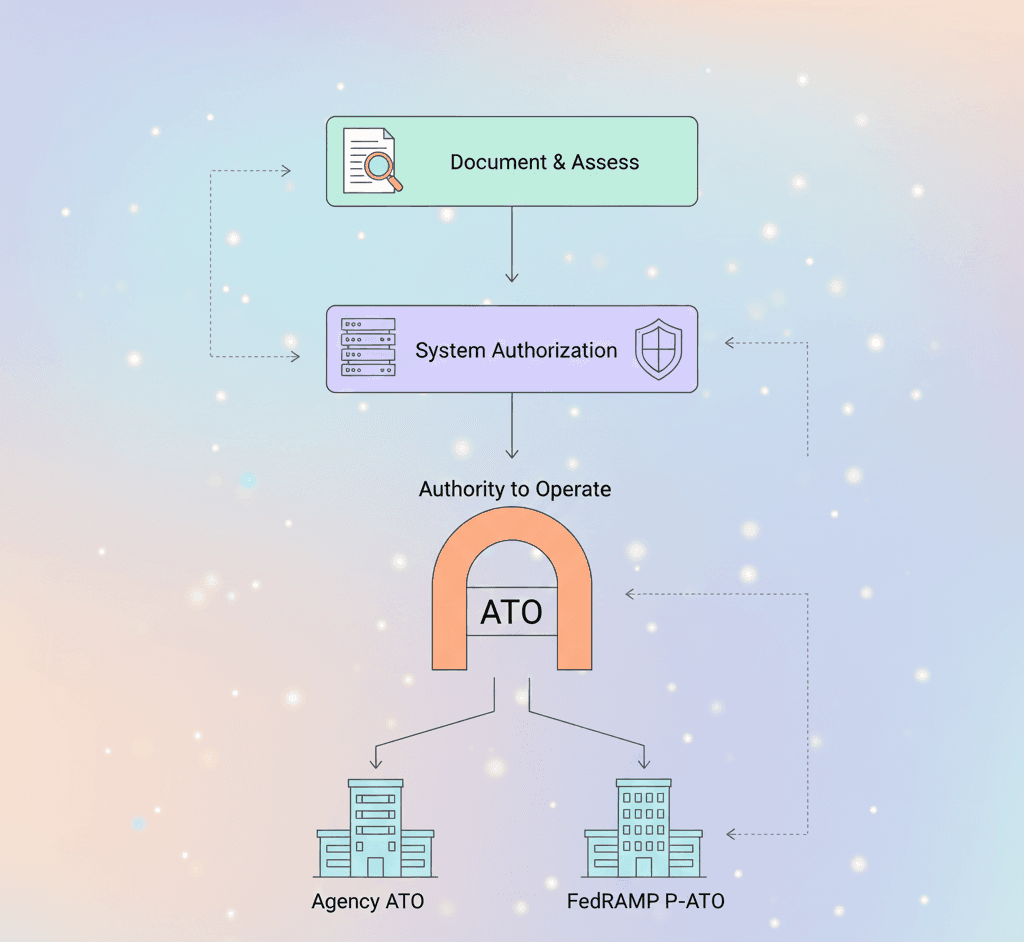
Vulnerability scanning is one of the most critical—and commonly misunderstood—requirements for achieving a FedRAMP Authorisation to Operate (ATO). Cloud Service Providers (CSPs) must demonstrate a robust and mature vulnerability management program to align with FedRamp security compliance and the broader FedRamp assessment expectations. That means implementing the right people, processes, and technologies to ensure continuous FedRamp security compliance.
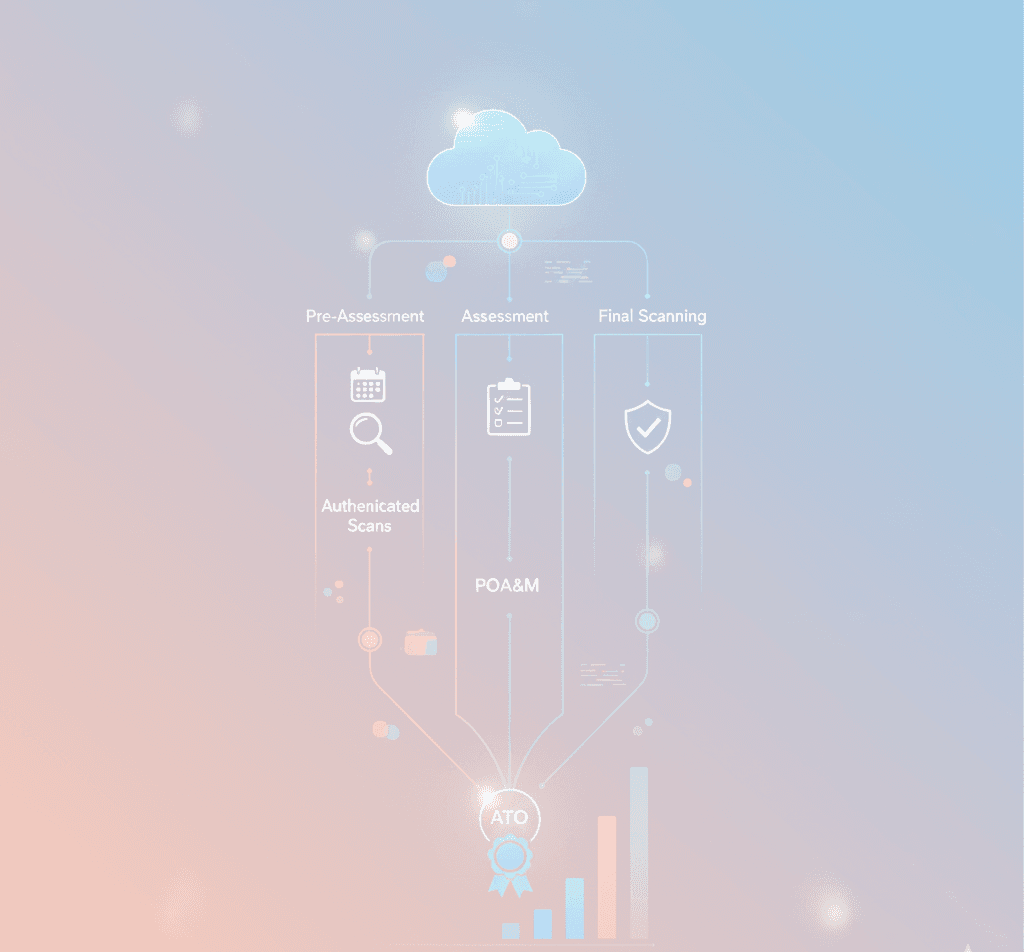
In this comprehensive guide, we’ll break down the FedRAMP vulnerability scanning process into three essential stages: pre-assessment, assessment, and final scans. We’ll also explore why this step is so important, highlight frequent missteps, and provide actionable insights to help your organisation avoid common pitfalls and accelerate your FedRamp audit.
What Is FedRAMP Vulnerability Scanning and Why Does It Matter?
Vulnerability scanning is a cornerstone of the FedRamp assessment process, used to evaluate how well a cloud system detects, manages, and mitigates known security weaknesses. It involves methodical scanning of cloud infrastructure, web applications, databases, and other in-scope components using authenticated and up-to-date scanning tools.
While it’s only one part of the overall FedRAMP assessment, vulnerability scanning has an outsized impact on whether a CSP is granted an ATO and on your FedRamp cloud certification readiness. It reflects your organisation’s ability to maintain secure configurations, remediate vulnerabilities quickly, and protect federal data across cloud environments.
Failing to follow proper procedures or submit sufficient documentation can significantly delay your FedRamp audit—or worse, result in denial of authorisation. That’s why implementing a mature, secure code review report, source code review in cybersecurity, and vulnerability management process is critical.
FedRAMP scanning requirements focus on:
Complete, authenticated scans across the entire system boundary
Timely remediation of high- and moderate-risk vulnerabilities
Accurate documentation of false positives, scan exceptions, and operational constraints
Use of secure code review reports and vulnerability data in machine-readable formats
Alignment with the FedRamp system security plan (SSP) and submission expectations for the FedRamp SAP
The Three Stages of FedRAMP Vulnerability Scanning
To align with FedRamp security compliance expectations, CSPs must adopt a phased, proactive approach to vulnerability scanning. Below are the three key stages, with goals, best practices, and common issues to watch for.
Stage 1: Pre-Assessment
60–90 days before your Security Assessment Report (SAR), provide your Third-Party Assessment Organisation (3PAO) with vulnerability scan data from the past three months. Scans should be exported in both native file formats and CSV to ensure compatibility with automated review tools and the FedRamp readiness assessment report process.
Key questions to address early:
Are scans authenticated with privileged credentials?
Are all plugins and checks enabled?
Are all components (infrastructure, containers, web apps, databases) included?
Who owns scan configuration and remediation responsibilities?
Are vulnerabilities being remediated within 30/90 days (high/moderate severity)?
Common pitfalls to avoid:
Unauthenticated scans: Lack of credentials can delay your fedramp audit for weeks.
Disabled plugins: FedRAMP expects all checks to be enabled unless performance degradation or other critical issues are formally documented.
Scan coverage gaps: Ensure the full boundary is scanned—including cloud storage, virtual machines, databases, and networking components referenced in your FedRamp system security plan.
Use this stage to proactively submit deviation requests and document false positives, operational exceptions, and risk-based adjustments. Doing this upfront reduces friction during your actual FedRamp assessment or FedRamp SAP submission.
Stage 2: Assessment
During the formal assessment, your 3PAO will validate your vulnerability management posture based on the data submitted. If you’ve completed a comprehensive pre-assessment or a formal FedRamp readiness assessment, this stage should go smoothly.
Core focus areas:
Current picture: What vulnerabilities exist right now?
Remediation validation: Are issues being addressed within FedRAMP timelines?
Adjustments: Has anything changed (tools, personnel, technology, environment)?
Red flags that trigger reassessment:
Changes in vulnerability scanning tools
Modifications to scan checks or policies
Personnel turnover in scan ownership
Changes in system architecture or hosting environments
3PAOs take a holistic view, assessing vulnerability patterns across the full environment—not just individual hosts—so CSPs should ensure broad remediation, not isolated fixes. Make sure your evidence ties back to the FedRamp system security plan and that findings are ready to be included in your FedRamp SAP.
Stage 3: Final Scan
Roughly 30 days after your initial Scans of Record, CSPs must submit a final round of scans showing that earlier findings have been remediated. This is the last opportunity to demonstrate compliance before the SAR is finalised and sent with your FedRamp SAP package.
Goals for final scans:
Remediation proof: Scans should clearly show that all vulnerabilities found in previous stages have been addressed.
Documentation: Ensure all risk adjustments (RAs), operational requirements (ORs), and false positives (FPs) are included in the Plan of Action and Milestones (POA&M).
Continuous monitoring readiness: Validate that no high-severity vulnerabilities remain and that your team is ready to submit monthly scan results moving forward.
Any unresolved high-severity findings must be tracked in your POA&M. This documentation becomes part of the official FedRamp audit record and supports ongoing FedRamp security compliance after your FedRAMP cloud certification or ATO.
Navigating FedRAMP Vulnerability Scanning with Confidence
FedRAMP compliance in 2025 and beyond continues to emphasise complete scan coverage, authenticated checks, and rapid remediation. A mature vulnerability management program—backed by effective tooling, accurate FedRamp SSP templates, and clear documentation—makes the difference between a smooth authorisation process and significant delays.
For more information on requirements, timing, and best practices for your FedRAMP vulnerability scans, review official FedRAMP guidance and prepare these artefacts for your fedramp readiness assessment and final FedRAMP SAP submission:
FedRamp assessment checklists and scan templates
fedramp system security plan alignment and fedramp ssp templates
Building evidence for your FedRamp readiness assessment report and SAR
Need Help with Your FedRAMP Assessment?
Accorp offers FedRamp assessment and FedRamp audit support, plus source code review services to help your organisation prepare for authorisation with confidence. Contact us today for help with:
Secure code review reports
Source code review in cybersecurity and end-to-end source code inspection
Full vulnerability scanning lifecycle support aligned to FedRamp security compliance and FedRamp cloud certification goals.