Everything You Need to Know About FedRAMP Pen Test Guidance 3.0
Everything you need to know about FedRAMP Pen Test Guidance 3.0—key updates, attack vectors, and compliance steps to prepare for your FedRAMP audit.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
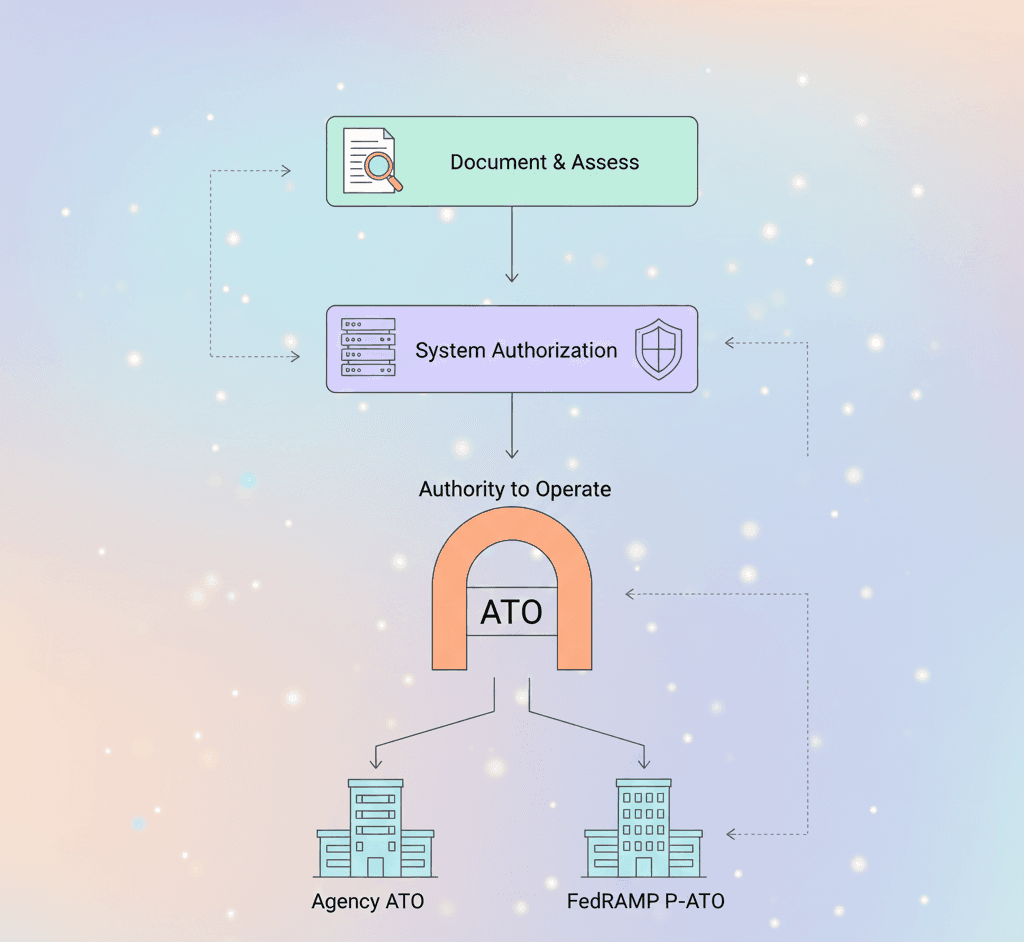
For the first time since 2017, the FedRAMP Program Management Office (PMO) has released an updated Penetration Testing Guidance document—version 3.0. For Cloud Service Providers (CSPs) seeking FedRAMP cloud certification and aiming to achieve or maintain a FedRAMP Authority to Operate (FedRAMP ATO), this update is crucial.
Understanding these changes is essential for staying in compliance during a FedRAMP assessment and ensuring successful outcomes during your next FedRAMP audit. At Accorp, we break down these updates to help you navigate the complexities of FedRAMP security compliance and streamline your path to certification.
What’s New in FedRAMP Penetration Testing Guidance 3.0?
Here are the key highlights:
Merged Attack Vectors: The Internal Network attack vector is now integrated with the External Network vector under a broader scope titled "Internal Threat Models."
Insider Threats Emphasised: CSPs and 3PAOs are required to assess and address insider threats more explicitly, although the guidance remains flexible in execution.
Production Environment Requirement: All testing must now occur in the production environment—no more using staging or QA setups.
Phishing Campaign Rules: The guidance is stricter on phishing assessments, requiring tests to bypass technical defences and mandating training and password changes for affected users.
Client-Side Testing Clarified: New direction on how client-side apps should be evaluated.
Detailed Breakdown of the Six FedRAMP Attack Vectors
1. External to Corporate (Phishing)
Objective: Assess how personnel respond to sophisticated phishing attacks.
Execution:
Provide the employee target list.
Bypass filters like email gateways.
Any data submitted during the campaign = test failure.
Remediation: Affected users must undergo security awareness training, and credentials must be rotated.
2. External to Target System (FedRAMP Boundary)
External Threats: Simulate uncredentialed Internet-based attacks.
Internal Threats: Validate how access from within the FedRAMP system security plan boundary is handled, checking controls, segmentation, and configurations.
3. Tenant to CSP Management System (Web Application)
Tests whether customer-facing portals can be exploited to compromise internal systems, which is crucial for your FedRAMP Security Assessment Plan (SAP) readiness.
4. Tenant-to-Tenant (Web Application)
Ensures customer data isolation and secure multi-tenancy—a core principle highlighted in every FedRAMP readiness assessment report.
5. Mobile Application to Target System (iOS & Android)
Focuses on encryption, logging, authorisation, and secure storage—important areas documented in your FedRAMP SSP templates and FedRAMP SAR.
6. Client-Side Application and/or Agents to Target System
Covers agents, browser extensions, and other client tools. During a FedRAMP readiness assessment, these components are often overlooked but can pose significant risks.
Key Considerations for FedRAMP Security Compliance
Test All Required Vectors: Missing any test without FedRAMP AO approval may result in a High Risk finding in the FedRAMP SAR.
Phishing Must Bypass Controls: Reminds CSPs that user behaviour and detection response form part of the FedRAMP audit.
Production Testing Only: Reinforces the importance of having a live, hardened architecture ready for evaluation.
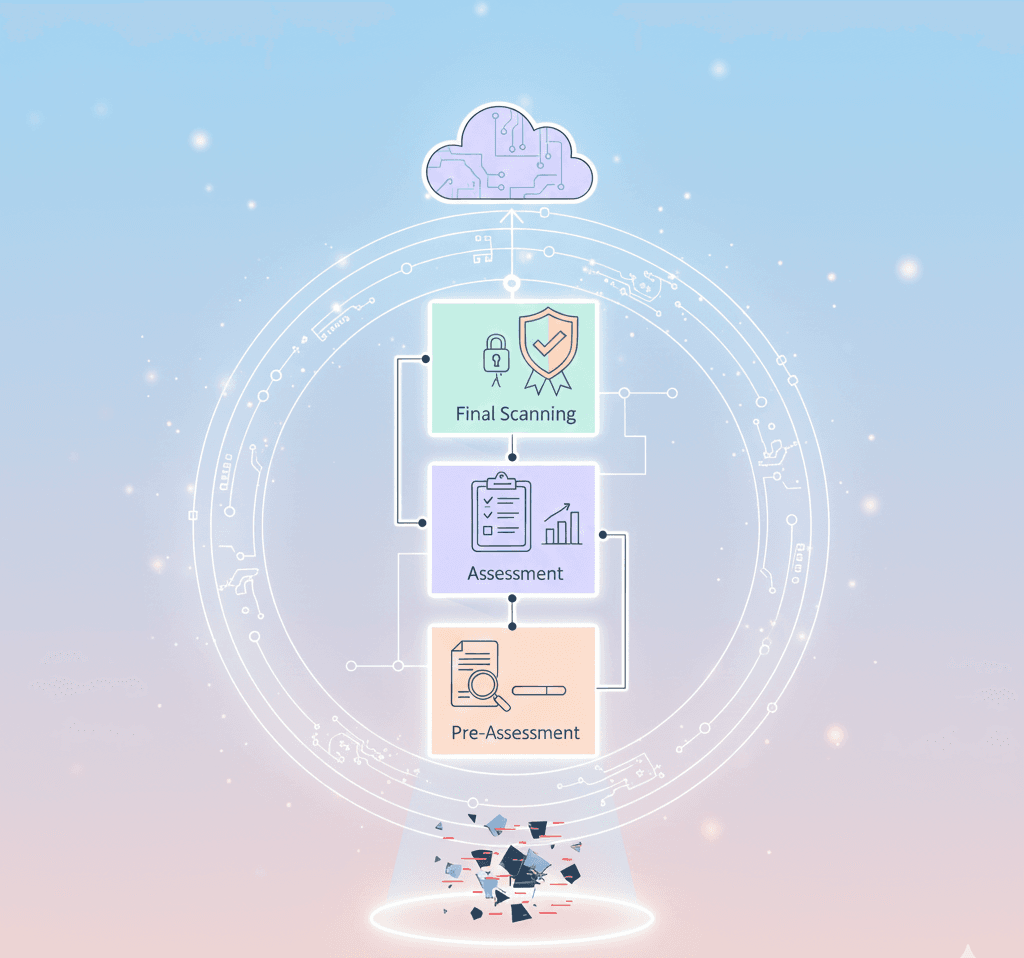
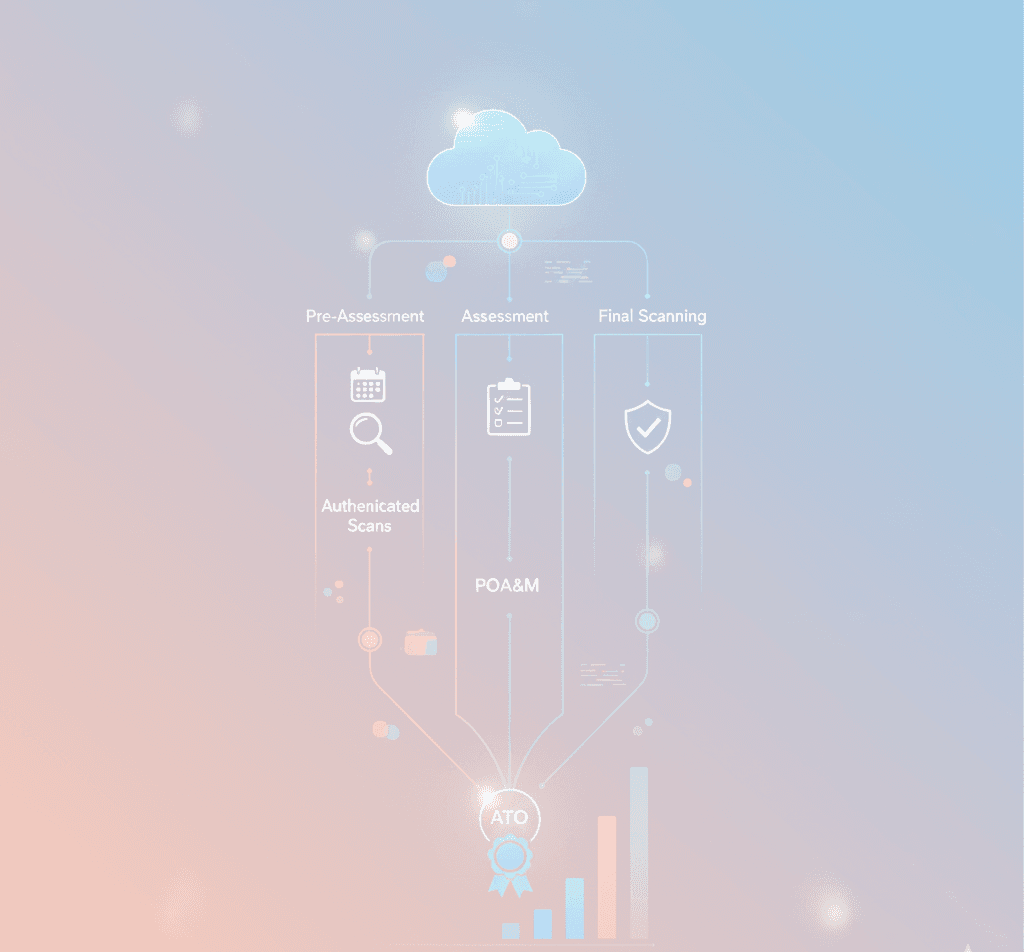
Next Steps for CSPs Preparing for a FedRAMP Assessment
Since August 22, 2022, all FedRAMP assessments must adhere to version 3.0 guidance. If a required vector cannot be executed, a formal non-conformance justification must be submitted to your Authorising Official (FedRAMP AO).
At Accorp, we help CSPs get ready with:
Tailored FedRAMP SSP templates
Comprehensive FedRAMP readiness assessment
Support with FedRAMP SAP and FedRAMP SAR documentation
Penetration test review and audit preparation
Conclusion
FedRAMP Penetration Testing Guidance 3.0 introduces directional changes in how vulnerability and threat modelling must be handled for cloud systems intended for federal use. From phishing to client-side attacks, staying aligned requires not just documentation—but practical, demonstrated compliance with live production systems.
With Accorp’s expert advisory services, your team can confidently tackle every stage of the FedRAMP cloud certification journey—from readiness assessments to full authorisation and beyond.