Penetration Testing for SOC 2: A Critical Step in Risk Management and Compliance
Strengthen SOC 2 compliance with penetration vulnerability testing to uncover hidden risks, validate controls, and enhance your organisation’s security.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
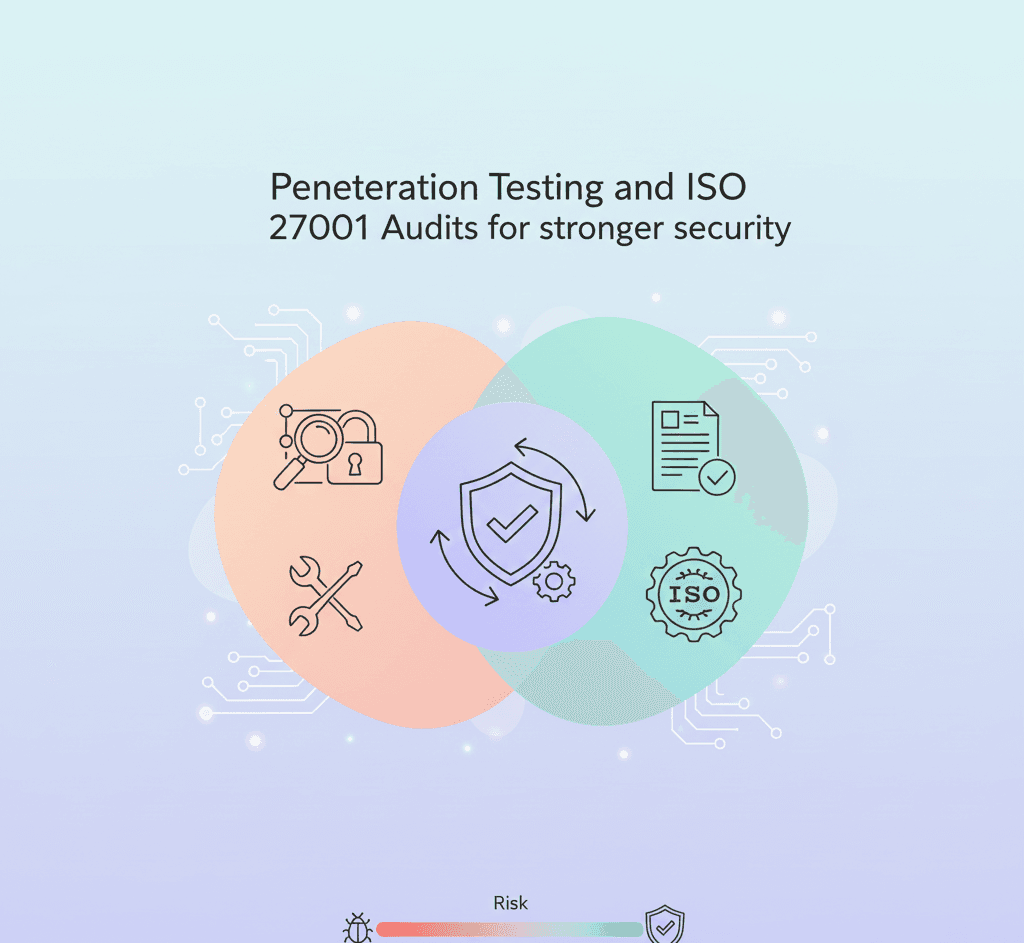
In today’s rapidly evolving cyber threat landscape, organisations must go beyond check-the-box compliance to protect sensitive data. At Accorp, we believe that combining penetration testing with SOC 2 audits is not just a best practice—it’s a strategic necessity for strengthening your security posture, mitigating risk, and achieving true compliance with Trust Services Criteria (TSC).
This powerful integration offers a comprehensive view of your organisation’s controls, exposing potential vulnerabilities and validating your defences through real-world attack simulations and a robust VAPT testing process. Here's why this combined approach should be part of your cybersecurity strategy.
What is SOC 2 and Why Does It Matter?
SOC 2 (System and Organisation Controls 2) is a framework developed by the American Institute of CPAs (AICPA) for managing customer data based on five Trust Services Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy.
A SOC 2 audit evaluates the design and effectiveness of your internal controls, ensuring you're managing data responsibly and securely. However, it typically focuses on policies, procedures, and documentation—leaving gaps in your actual technical defences.
The Missing Piece: Penetration Testing
While a SOC 2 audit reviews what should be happening in your environment, a penetration test (or pen test) evaluates what could go wrong if attackers target your systems. Using tools like a pentest scanner and experts like a penetration & vulnerability tester, a pen test simulates real-world attacks to uncover hidden penetration testing vulnerabilities—such as misconfigured servers, insecure APIs, or weak access controls—that compliance checks may miss.
Pen testing dives deep into your networks, applications, and endpoints, and may also include a pentest website online or an API free test to check common entry points that attackers probe.
5 Reasons to Combine Penetration Testing with Your SOC 2 Audit
1. Comprehensive Security Assessment
SOC 2 provides a top-down view of your controls, but penetration testing gives you a bottom-up perspective—highlighting technical weaknesses at the configuration or code level.
Tools like Check My API tests or penetration testing OWASP Top 10 frameworks ensure you catch common issues like injection flaws or misconfigured authentication.
2. Validation of Security Controls
Security controls are only effective if they withstand real-world attacks. Penetration testing validates your SOC 2 controls under pressure—whether it’s simulating phishing attempts, SQL injection attacks, or exploiting configuration flaws.
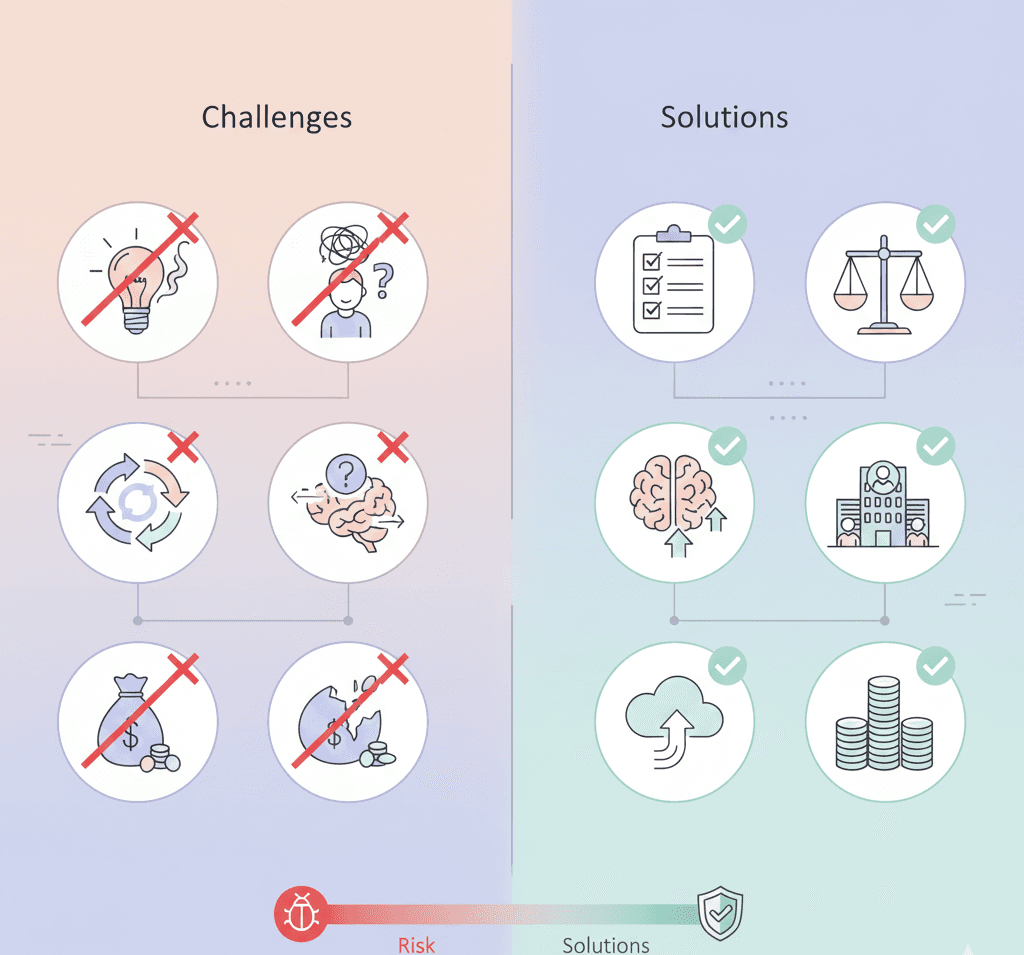
3. Proactive Risk Mitigation
Pen tests find weaknesses before attackers do. For instance, discovering a SQL injection vulnerability or cross-site scripting flaw allows your team to fix it before it becomes a serious threat.
This proactive approach aligns with an effective penetration vulnerability testing strategy and reduces the chance of incidents that might result in legal, financial, or reputational damage.
4. Enhanced Compliance with Trust Services Criteria (TSC)
Each SOC 2 TSC pillar benefits from integration with penetration testing:
Security: Spot unauthorised access points via tools like pentest scanners
Availability: Simulate DDoS or server overload scenarios
Confidentiality: Expose unencrypted sensitive data
Processing Integrity: Check logical flaws in transaction flows
Privacy: Confirm secure handling of PII and API inputs with check my API
5. Continuous Improvement & Long-Term Resilience
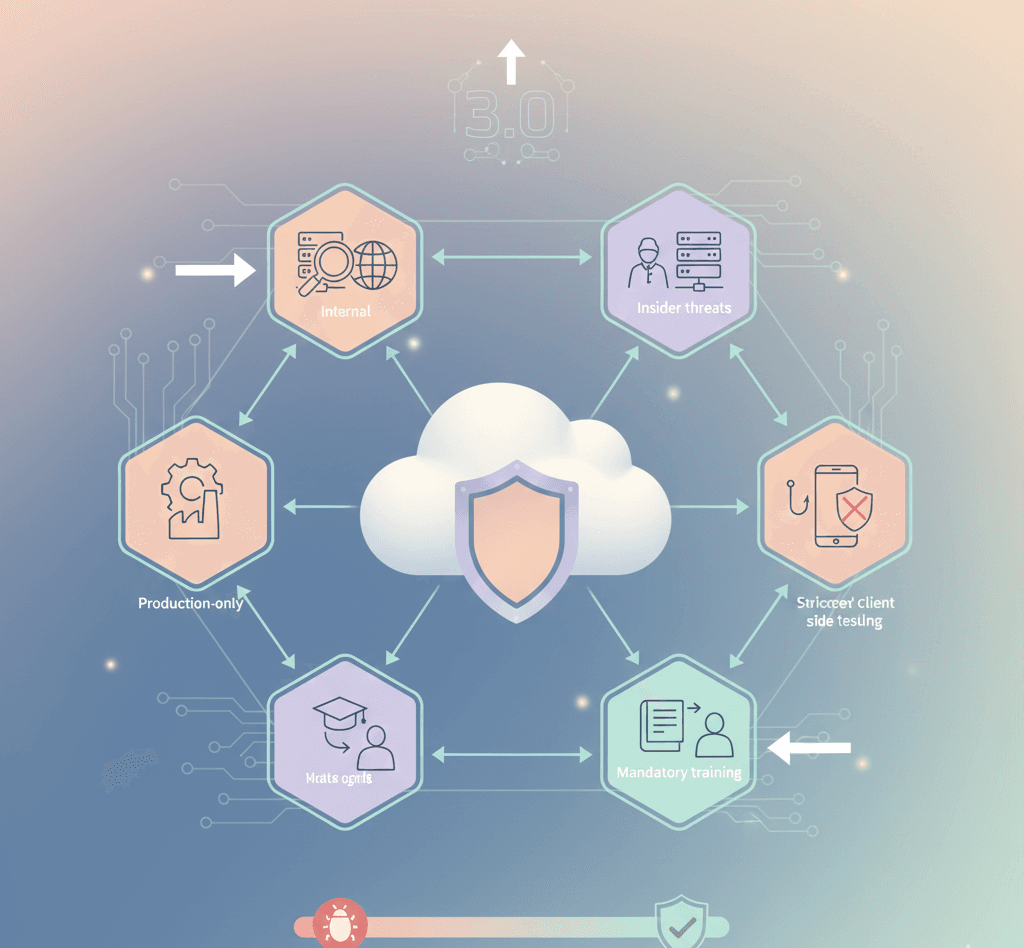
With cyber threats constantly evolving, regular penetration testing creates a feedback loop that goes beyond SOC 2’s requirements—feeding directly into your risk management and DevSecOps processes.
This helps your organisation build long-term resilience and stay agile in a dynamic threat environment.
The Competitive Advantage for Accorp Clients
At Accorp, we help organisations build security programs that go beyond compliance. By integrating penetration testing into your SOC 2 readiness or audit process, we deliver a performance-driven security assessment that ensures:
Effective control implementation
Real-world risk identification
Reduced the likelihood of security incidents
Enhanced trust and confidence for your customers and auditors
This combined approach also positions you for success under other frameworks such as ISO 27001, HIPAA, PCI DSS, or even NIST and GDPR.
If your organisation is planning for a SOC 2 audit or looking to enhance your cybersecurity posture, now is the time to add penetration testing to your roadmap.
At Accorp, our experts provide tailored VAPT testing, SOC 2 consulting, and offensive security services—all aligned to make your security smart, strong, and sustainable.