How to Combine Penetration Testing and ISO 27001 Audits for Stronger Security
Enhance ISO 27001 compliance by combining audits with penetration testing. A penetration & vulnerability tester helps validate controls and strengthen security.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
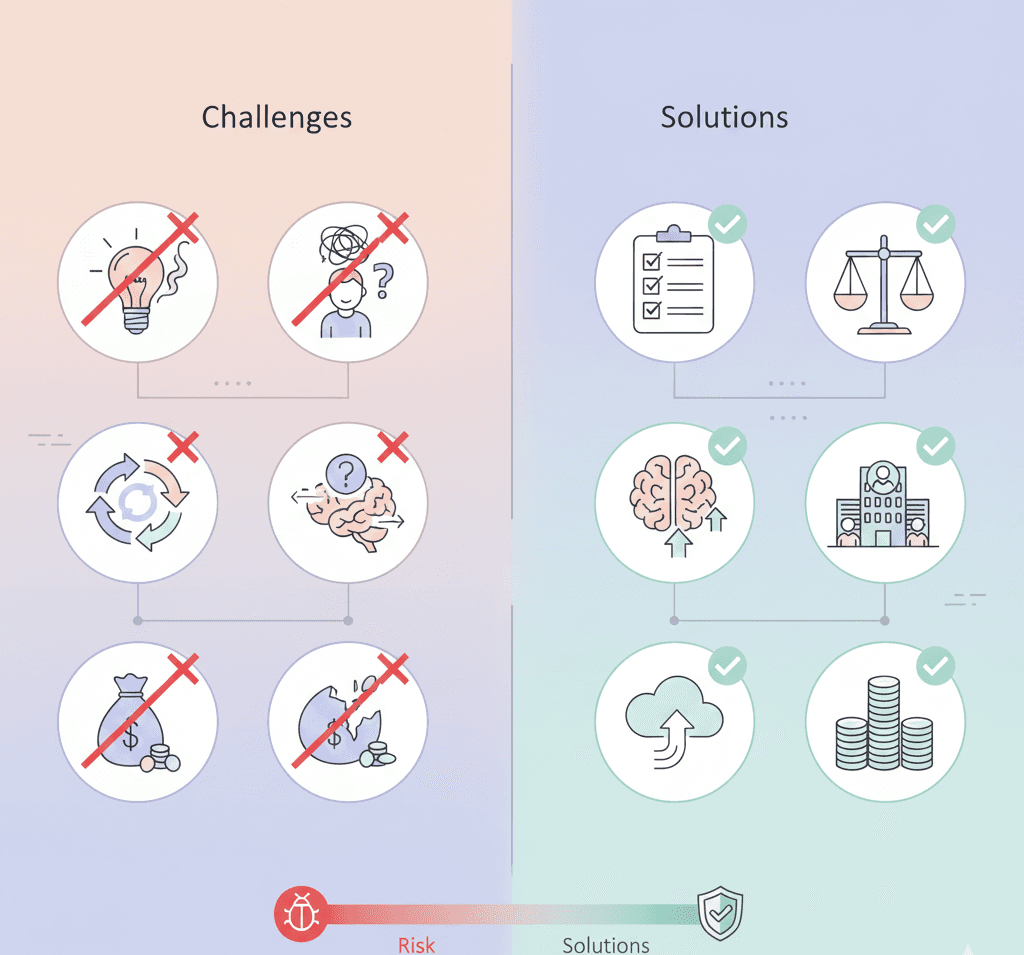
Cybersecurity frameworks and compliance standards are essential for safeguarding sensitive data—but policies and procedures alone don’t guarantee resilience. While an ISO/IEC 27001 audit helps establish a strong foundation for information security through structured governance and risk management, it doesn’t simulate how a system would perform under real attack conditions.
This is where penetration testing becomes a valuable complement. By mimicking tactics used by malicious hackers and leveraging a VAPT testing process, penetration tests expose real vulnerabilities that internal controls may overlook. When conducted alongside an ISO 27001 audit, penetration testing provides both a strategic and technical lens on your security program—ensuring it’s not only well-documented but also truly battle-tested.
5 Key Benefits of Integrating Penetration Testing with ISO 27001 Audits
1. Stronger Risk Management
ISO 27001 mandates a structured approach to identifying and treating risks. Penetration testing supports this by exposing hidden penetration testing vulnerabilities that formal risk assessments may miss. This helps organisations proactively reduce their attack surface and enhance mitigation strategies.
2. Enhanced Compliance Confidence
ISO 27001 Annexe A recommends regular vulnerability assessments and technical testing. Penetration testing—including targeted penetration vulnerability testing with tools like a pentest scanner—directly supports this, providing documented evidence of security validation efforts. This strengthens your audit trail and builds trust with stakeholders, clients, and regulatory bodies.
3. Validation of Security Controls
Security controls—like access restrictions, encryption, and incident response procedures—are only effective if they work under real pressure. Pen testing tests these controls in action, typically covering penetration testing OWASP Top 10 risks for applications, Facility Penetration Testing for physical security, and more. This allows your team to fix issues before attackers find them.
4. Better Incident Response Readiness
Penetration testing provides a live-fire exercise for your incident response team. Whether it’s a simulated phishing attack or an external penetration & vulnerability tester uncovering cloud misconfigurations, it exposes how quickly and effectively your organisation can detect, respond to, and recover from incidents—insights that an audit alone won’t provide.
5. Continuous Improvement
ISO 27001 emphasises continuous improvement of security practices. As you refine your ISMS, repeated penetration testing (including convenient methods like pentest website online and check my API tools or API free test utilities) gives your organisation feedback loops—highlighting not only what went wrong but also how your security posture evolves.
When Should You Conduct a Penetration Test During an ISO 27001 Audit?
Before the Audit: Identify and remediate issues early so your ISMS is both compliant and hardened.
During the Audit: Validate technical controls in real-time as your auditor reviews policies.
After the Audit: Use audit findings to guide the scope of a post-audit penetration test or advanced VAPT testing process.
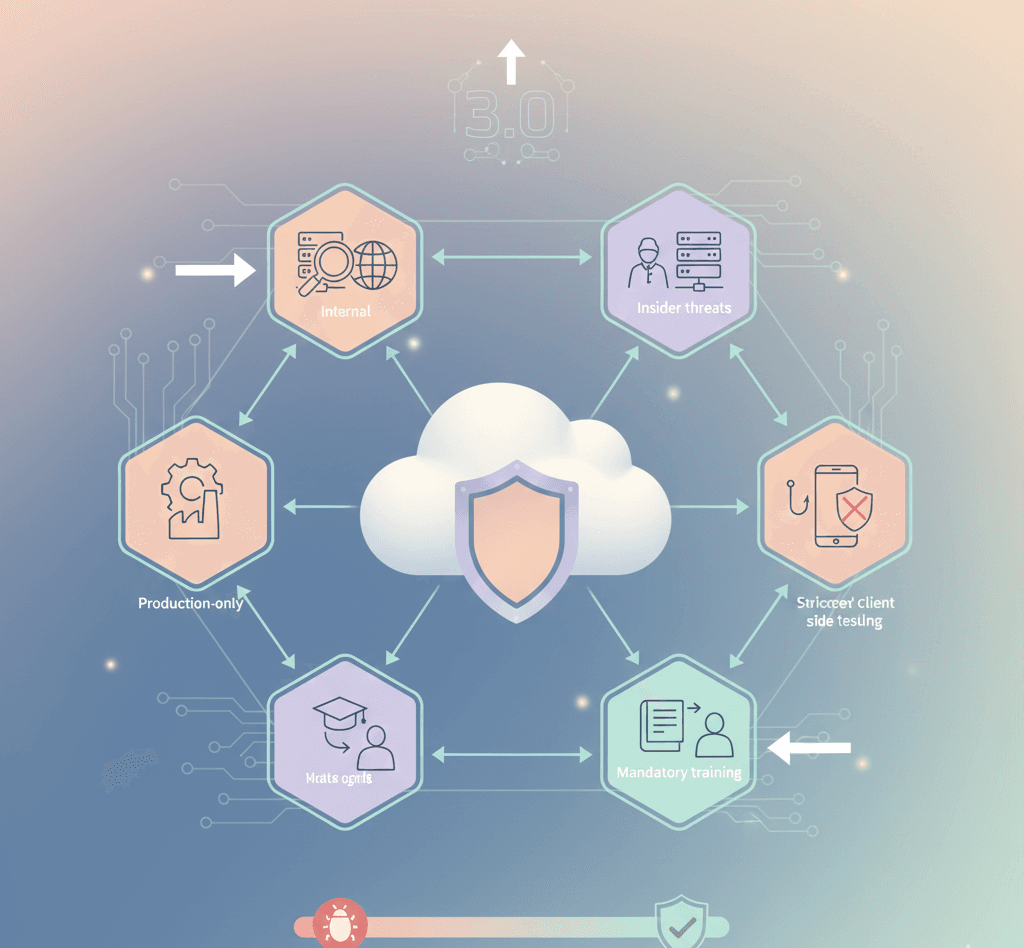
What Areas Should Your Penetration Test Cover?
A robust pen test aligned with ISO 27001 objectives typically includes:
Network Security – Test firewalls, routers, switches, and VPNs
Web and Mobile Applications – Simulate OWASP-based attacks
Cloud Environments – Evaluate misconfigurations and access controls
Internal Systems – Test access privileges and lateral movement
APIs and Microservices – Run check my API scans or API free test tools
Physical Security – Assess entry controls via Facility Penetration Testing
Human Factor – Simulate social engineering or phishing attacks
Why Accorp Recommends This Combined Approach
At Accorp, we help organisations of all sizes achieve ISO 27001 certification while building practical, resilient cybersecurity strategies. We recommend integrating penetration testing into your ISO audit process because it provides a real-world validation of your controls—not just paperwork or policy checks.
With our experts by your side, supported by cutting-edge pentest scanner tools and a deep understanding of real-world attacks, you’ll gain insights that lead to faster improvements, stronger compliance, and greater peace of mind.