From Gaps to Guardrails: A Pen Testing Readiness Checklist
Prepare your organisation for a successful security assessment and address penetration testing vulnerabilities with this complete readiness checklist.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
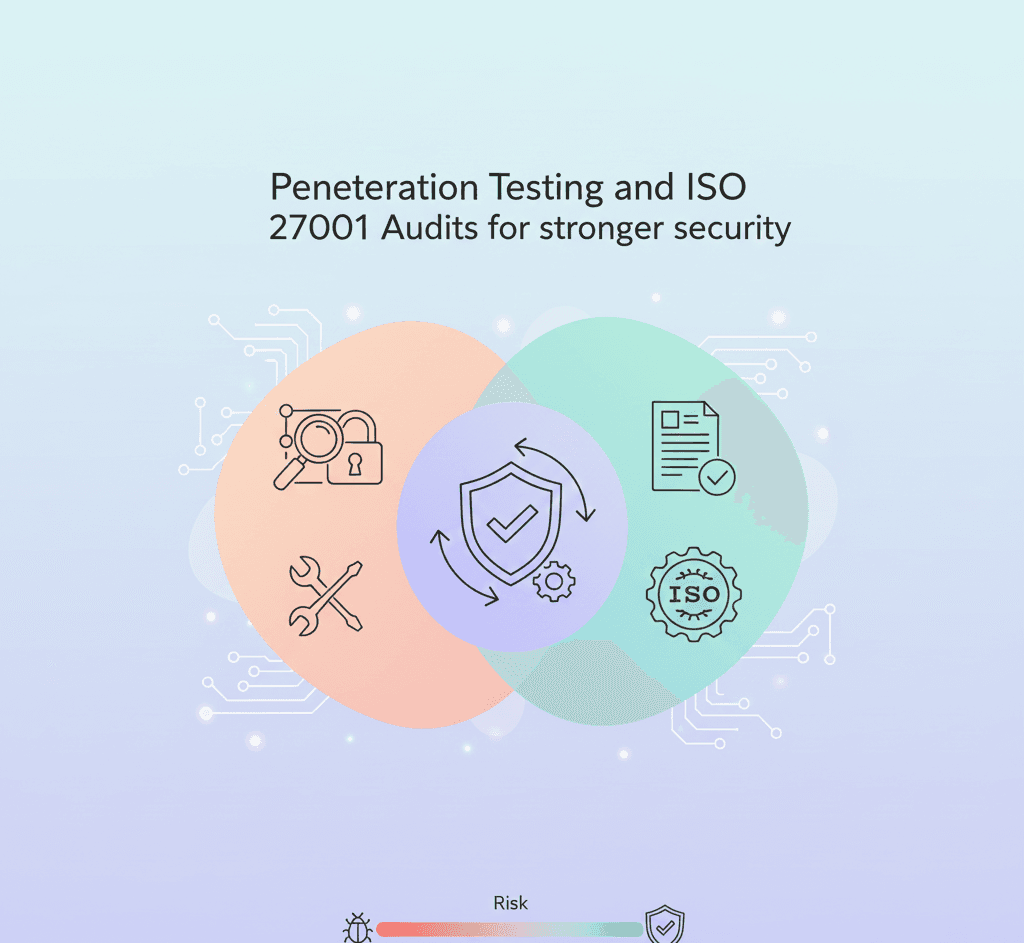
Penetration testing, or ethical hacking, is a vital part of modern cybersecurity. It simulates real-world attacks on your systems to identify weak points before malicious actors do. But the value of a penetration test doesn’t lie in the test itself—it lies in how well your organisation is prepared to undergo it.
At Accorp, we believe preparation isn’t just a checklist—it’s a mindset. A well-prepared organisation will get the most accurate, useful results from their penetration testing engagement. This article walks you through a full readiness roadmap so you can strengthen your cybersecurity posture, minimise test disruptions, and maximise the value of every test cycle.
Why Penetration Testing Preparation Matters
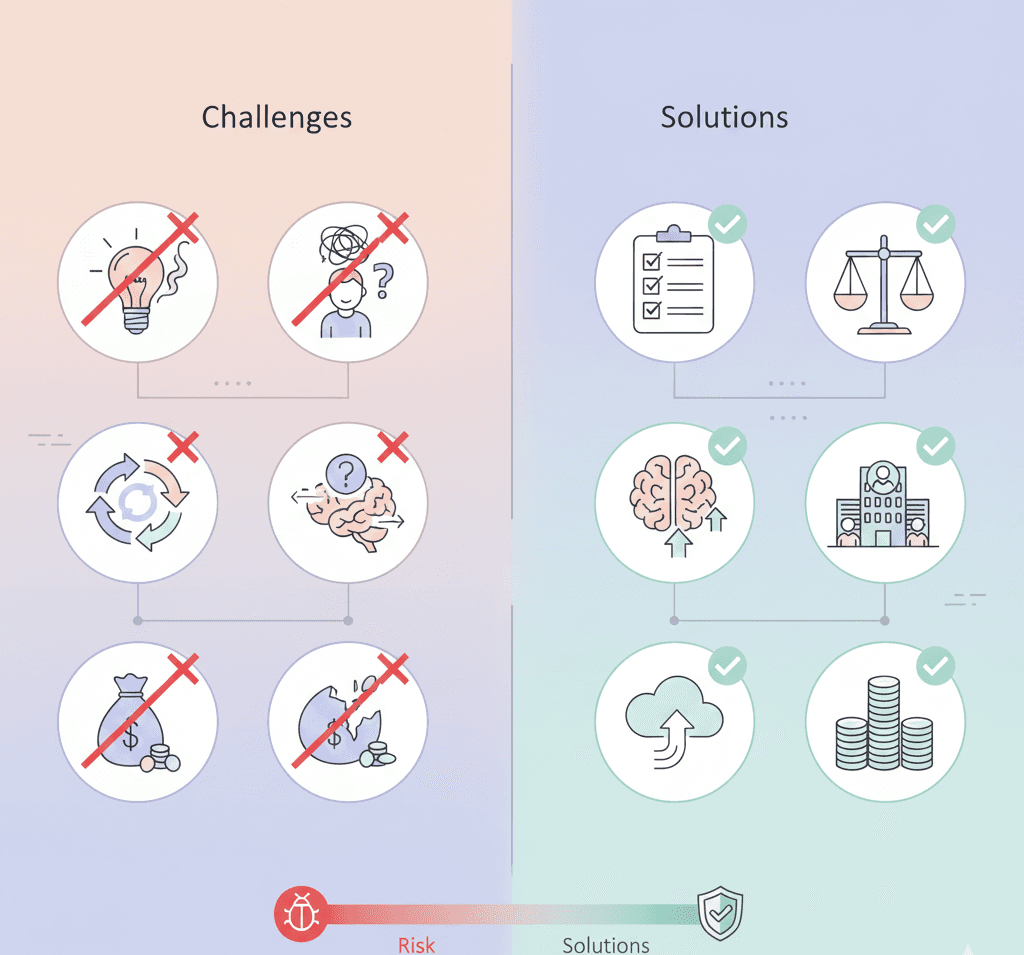
Jumping into a pen test without proper planning is like racing into battle without armour. Preparation ensures that your team, technology, and procedures are aligned with both industry best practices and your internal security goals. A strong preparation strategy will help you:
Align testing with your business and security objectives
Identify existing blind spots in your systems and processes (including common penetration testing vulnerabilities)
Enable teams to respond efficiently during and after testing
Avoid operational disruptions or compliance issues
Penetration Testing Readiness: Your Action Plan
Here’s a detailed breakdown of what your organisation should do before engaging a penetration testing provider. For a complete and downloadable checklist, visit our resource centre.
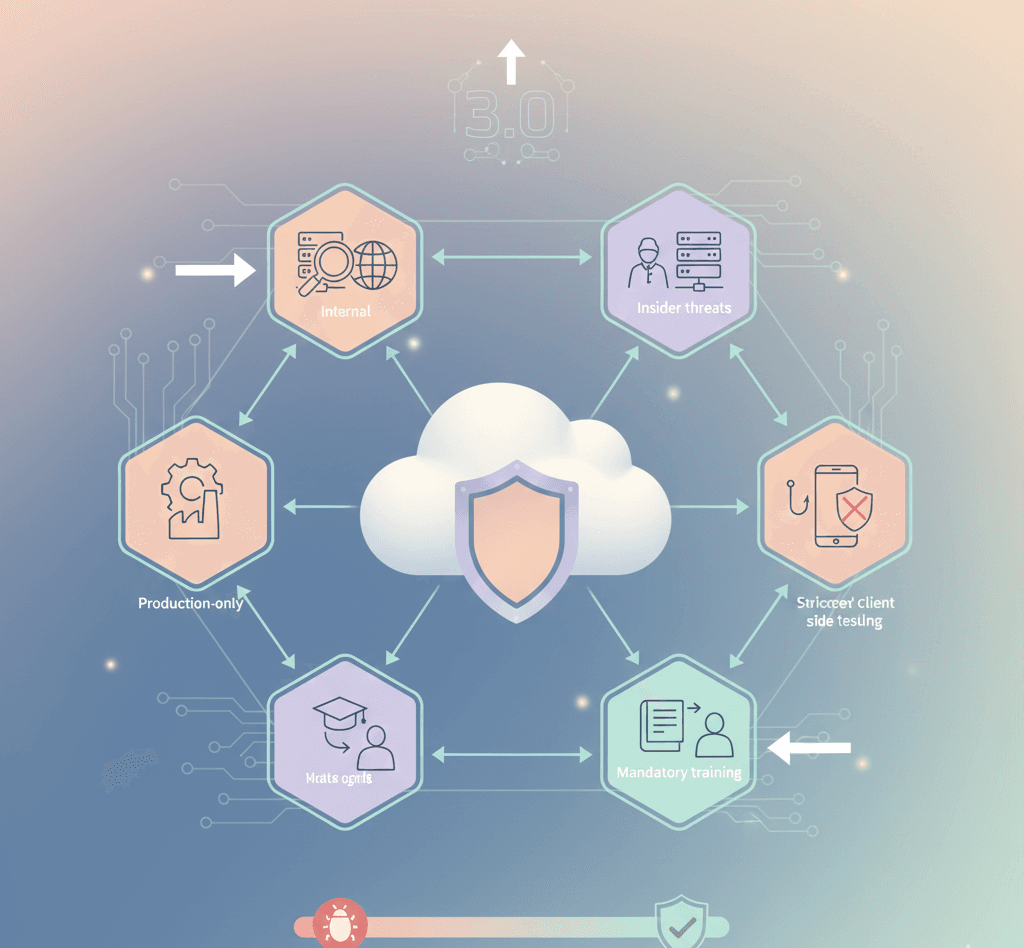
1. Organisational Readiness
Define Clear Objectives — Why are you conducting a pen test—compliance, risk management, system hardening, or all the above? Clearly document your goals, and decide whether you’ll include a full vapt testing process or a focused penetration exercise.
Map Out Roles and Responsibilities — Make sure everyone knows their part—executives, IT, compliance officers, and system owners should be looped in from day one.
Assign Oversight — Secure leadership buy-in and budget approvals. Executive oversight ensures accountability and smooth decision-making.
Maintain Proper Separation of Duties — Avoid conflicts of interest—testing should be conducted independently from development or operations teams to ensure unbiased results. Consider engaging an external penetration & vulnerability tester if impartiality is required.
2. Policies & Governance
Update Your Security Policies — Ensure your information security policy reflects current standards and is readily available to all staff.
Implement and Communicate Procedures — From employee handbooks to code of conduct documents—train your staff on acceptable behaviour and security expectations.
Schedule Security Awareness Training — Regularly educate teams on phishing, password hygiene, and evolving threats. An informed team is your first line of defence.
Conduct Regular Personnel Evaluations — Assess your staff’s readiness and adherence to security protocols with periodic reviews.
3. Technical Environment Review
Inventory All Assets — List all hardware, software, cloud platforms, APIs, and endpoints to ensure full visibility. If you expose APIs, add them to the scope and use tools or services to check my API or run an api free test as part of initial discovery.
Provide System Architecture Documentation — Pen testers need accurate diagrams and documentation to navigate your environment effectively.
Conduct Preliminary Vulnerability Scans — Scanning beforehand helps you understand your baseline and fix low-hanging fruit before deeper testing begins, using both automated pentest scanner tools and manual checks.
Classify Sensitive Data — Identify and tag critical data types—like PII, cardholder data, or health records—to prioritise their protection during the test.
4. Testing Environment & Controls
Establish Testing Windows — Coordinate with IT to select timeframes that minimise operational disruption and ensure coverage of high-risk periods.
Inform Third-Party Vendors — If any system in scope involves outsourced services or cloud infrastructure, align with your vendors on test timing and scope.
Secure Legal Authorisation — Always ensure written permission is in place to conduct penetration testing—especially for externally hosted systems.
Define Test Scope Clearly — Avoid ambiguity. List exactly what’s in scope for testing to protect critical infrastructure and ensure test accuracy. Clarify whether you want a comprehensive penetration vulnerability testing exercise or a limited assessment.
Notify Clients or Partners — If testing may cause visible service disruptions, provide proactive notice to build trust and transparency.
5. Team Readiness & Mental Preparation
Evaluate Security Team Skills — Do your internal teams have the expertise to understand pen test results? If not, consider external consultants or upskilling.
Close Skill Gaps — For complex environments, it may be necessary to bring in specialists in areas like cloud security or application testing. A certified penetration & vulnerability tester or dedicated VAPT provider can help bridge gaps.
Reframe the Test as Learning — Promote a positive culture around testing—focus on growth, not blame.
Address Team Burnout — Testing and remediation can be stressful. Provide mental health resources and realistic timelines for action.
6. Post-Test Strategy
Document Findings Thoroughly — Make sure your testing partner provides detailed reporting—what was found, where it exists, and how it was exploited. Reports should call out any penetration testing vulnerabilities and map them to frameworks such as the penetration testing OWASP Top 10.
Prioritise and Plan Remediation — Use a risk-based approach to address vulnerabilities. Start with critical issues, then tackle the medium- and low-risk items.
Execute Short-Term Fixes Promptly — Some vulnerabilities require urgent patches—don’t delay.
Implement Long-Term Improvements — Use testing insights to inform ongoing architectural changes, process improvements, and security policy updates.
Technical Add-Ons & Tools to Consider
Use an end-to-end vapt testing process that combines automated scans (pentest scanner) and manual exploitation.
Include API-specific checks: run pentest website online tools for public web apps and API fuzzers, or api free test utilities for endpoints.
Engage tools and specialists who can demonstrate coverage of penetration testing OWASP Top 10 threats (SQLi, XSS, etc.) and who document penetration vulnerability testing findings clearly.
The Bigger Picture: Turning Readiness Into Resilience
Penetration testing readiness isn’t just about compliance—it’s about strengthening your ability to respond, recover, and evolve. At Accorp, we help businesses turn pen testing into an ongoing tool for growth, security, and peace of mind. Whether you're preparing for your first assessment or refining an established security program, our team can guide you every step of the way.