Is Your Cloud Service C5 Compliant? Here’s What You Need to Know
Achieve strong cloud security with BSI C5 certification. Learn requirements, Type 1 vs Type 2, SOC 2 alignment, and steps for full C5 compliance.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
With the rapid evolution of cloud technologies, organisations face increasing pressure to meet strict security and compliance expectations. For cloud service providers (CSPs), proving their commitment to data protection and regulatory standards is no longer optional—it's a competitive necessity.
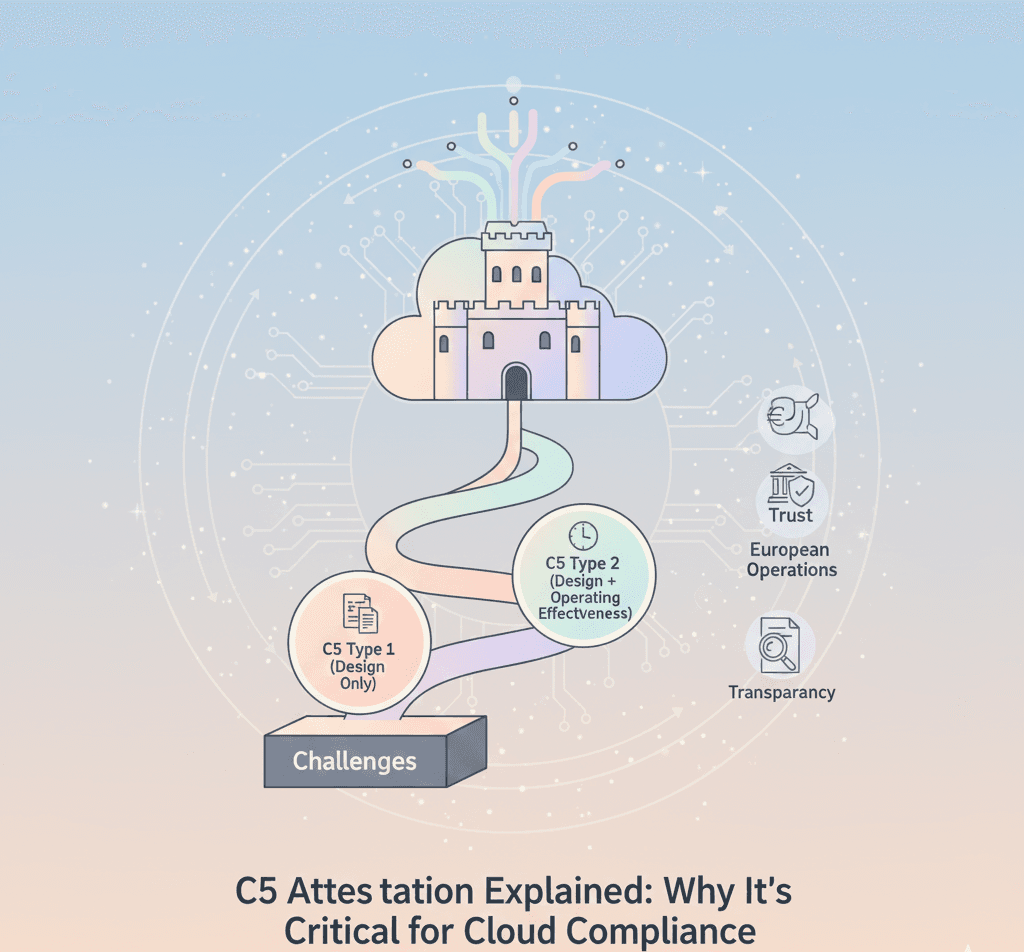
That’s where C5 attestation comes in. Developed by Germany’s Federal Office for Information Security (BSI), the Cloud Computing Compliance Criteria Catalogue (C5) offers a comprehensive framework that helps CSPs demonstrate robust cloud security practices. Whether you're aiming for BSI C5 certification, enhancing trust, or achieving C5 cloud compliance, understanding the C5 framework is essential.
What Is C5 Certification?
C5 certification is an independent attestation that verifies whether a cloud service provider complies with specific technical and organisational requirements for secure cloud computing. It’s particularly important for CSPs operating in Europe—or those working with European customers—because BSI C5 certification is increasingly accepted as proof of alignment with EU and German data-protection standards.
The C5 catalogue aligns closely with globally recognised standards such as ISO 27001/27017, AICPA Trust Services Criteria, and the Cloud Security Alliance’s CCM—allowing CSPs who already meet those frameworks to streamline their path to C5 cloud certification.
Why C5 Attestation Matters
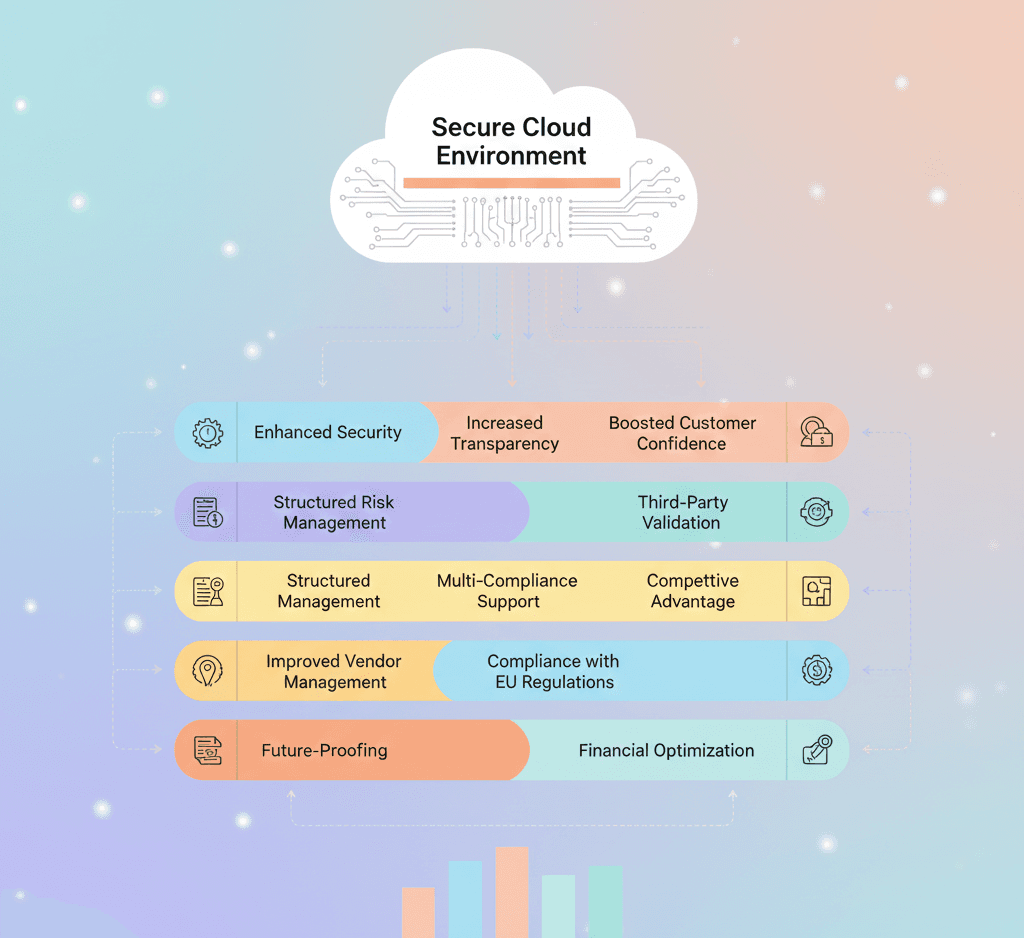
Pursuing C5 attestation delivers clear business benefits:
Strengthened Market Position: A BSI C5 certification signals commitment to cloud security—helpful when selling into regulated markets.
Reduced Risk Exposure: C5 requires rigorous documentation and operational controls that help identify and remediate vulnerabilities.
Regulatory Alignment: Sectors such as healthcare, finance, and government increasingly expect C5 compliance as a baseline.
Competitive Advantage: A verified C5 cloud certification distinguishes your service from non-certified competitors.
Core Requirements & Control Domains
The C5 catalogue is structured around 17 control domains (mapped to ISO Annexe A) covering topics such as:
Asset & configuration management
Physical & environmental security
Identity & access management
Logging, monitoring & incident response
Data protection, availability, and resilience
C5 adds cloud-specific requirements—data location controls, multi-tenant transparency, and service availability obligations—making it highly relevant for modern CSP architectures.
The C5 Examination Process (ISAE 3000 C5 & Types)
C5 assessments are performed using established assurance standards. Many audits are executed under ISAE 3000 C5 engagements and may reference AT-C guidance where applicable. There are two primary engagement types:
C5 Type 1 (Design Only): Evaluates the design and documentation of controls at a point in time. Good for startups and early-stage CSPs to demonstrate control intent.
C5 Type 2 (Design + Operating Effectiveness): Tests control operation over a defined period (commonly 6–12 months). Increasingly required by enterprise customers and regulators, C5 Type 1 vs Type 2 is therefore a pivotal decision for CSP roadmaps.
Recent regulatory updates mean that certain sectors will soon accept only C5 Type 2 certificates for compliance—so planning for Type 2 readiness is often prudent.
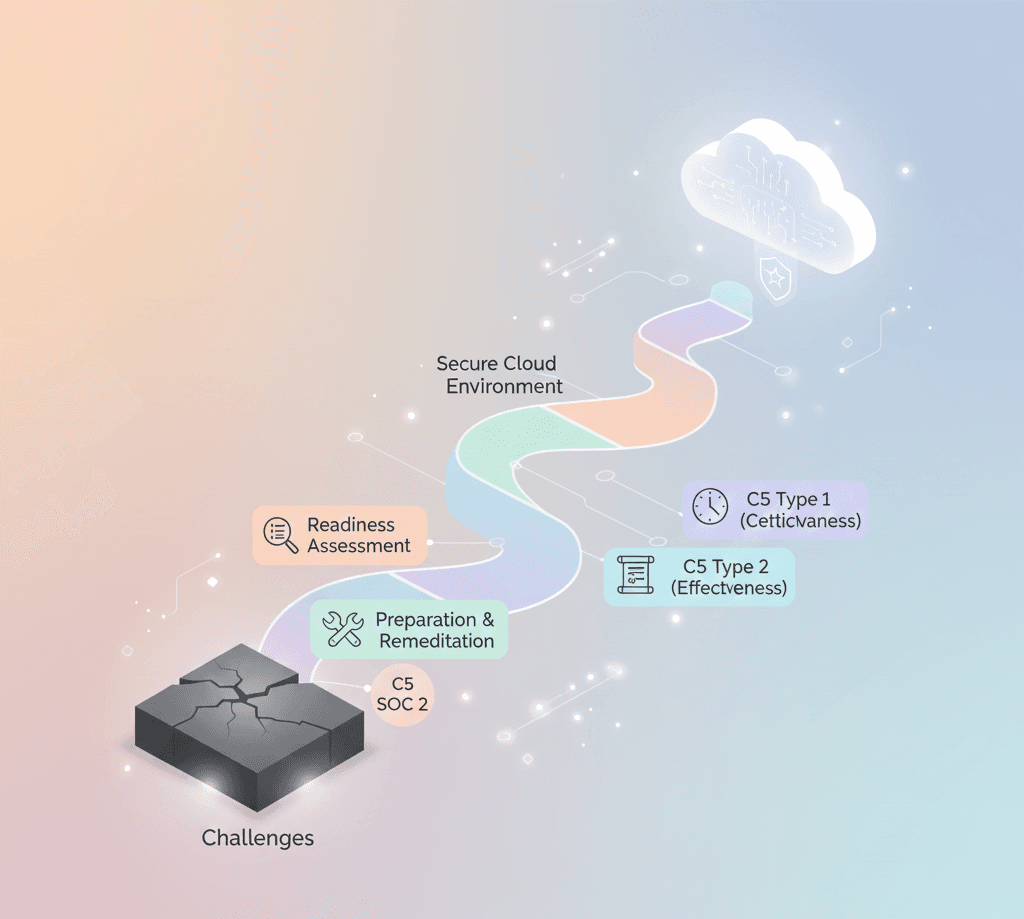
Practical Path: SOC 2 + C5 Readiness
Many providers use a combined approach—running a C5 SOC 2 readiness assessment or a SOC 2 + C5 roadmap—to minimise duplicate evidence collection. Typical steps include:
Perform a SOC 2 + C5 SOC 2 readiness assessment to map existing controls to both frameworks.
Close gaps in policies, IAM, logging, and encryption.
Execute a Type 1 engagement (if needed) to validate control design.
Progress to C5 Type 2 for operational assurance and broader market acceptance.
This combined route is particularly effective for CSPs that already maintain SOC 2 or ISO 27001 programs.
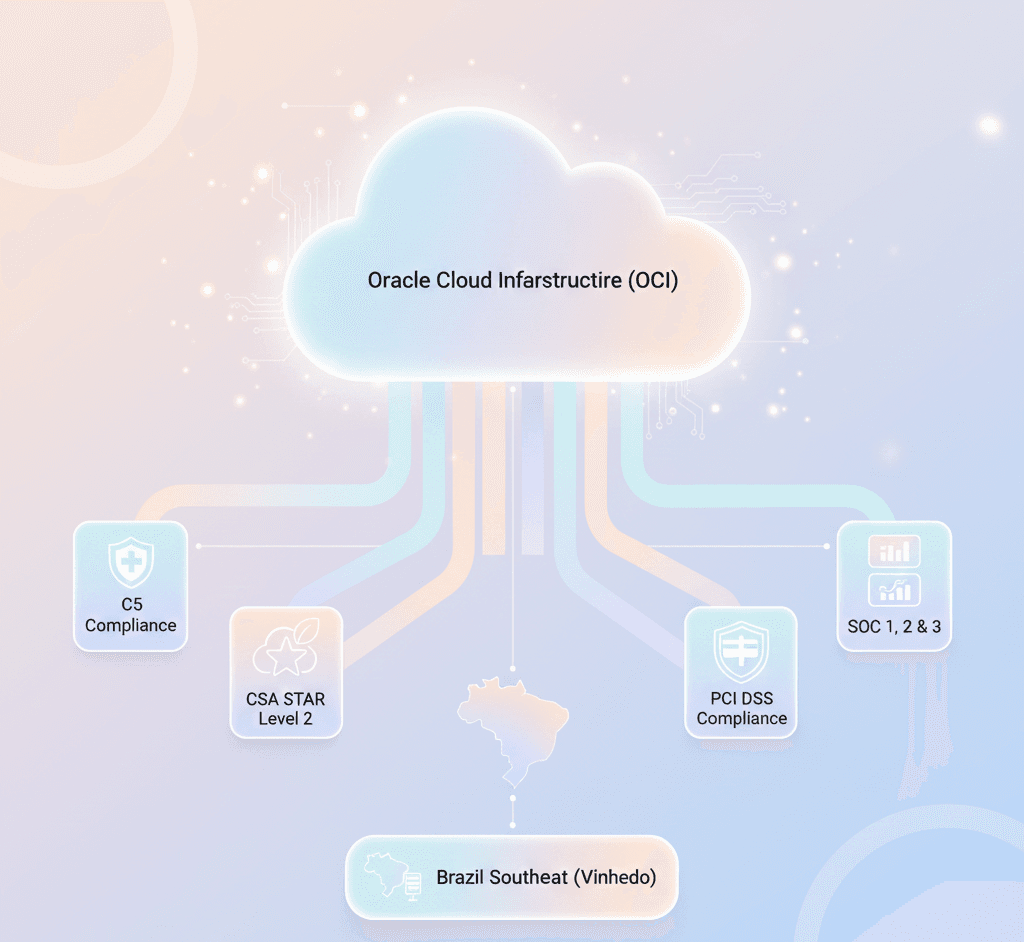
Regional Considerations: BSI C5 AWS & Data Residency
Some cloud customers require platform-specific assurances (for example, BSI C5 AWS) or guarantees about data residency. If you run services on hyperscalers like AWS, Azure, or Google Cloud, plan to:
Map your cloud architecture to C5 controls (shared responsibility model).
Leverage CSP attestation artefacts and region-specific compliance features.
Demonstrate contractual and technical measures for EU/EES data residency when required.
Getting Started: Roadmap to C5 Cloud Compliance
To pursue C5 cloud compliance, follow a structured approach:
Gap Assessment: Baseline controls vs C5 requirements (use ISAE 3000 C5 criteria where relevant).
Remediation Plan: Prioritise control fixes that reduce material risk and satisfy auditors.
Evidence Collection: Harden logging, change management, and access records for Type 2 readiness.
Audit Execution: Engage a qualified assurance firm for Type 1 or C5 Type 2 audits.
Continuous Improvement: Maintain controls and plan annual re-assessment or surveillance.
Why Accorp?
Accorp supports CSPs through every stage of C5 attestation and C5 cloud certification—from SOC 2 + C5 readiness assessments to full Type 2 audits. Our services include:
ISAE 3000 C5 advisory and audit coordination
SOC 2 + C5 control mapping and remediation planning
Evidence collection support for C5 Type 1 vs Type 2 timelines
Guidance on platform-specific proofs (e.g., BSI C5 AWS) and data residency clauses
Conclusion
C5 is rapidly becoming the benchmark for secure cloud services in Europe. Whether you need C5 attestation to win regulated customers, want to combine SOC 2 and C5 for audit efficiency, or are preparing for the new Type 2 expectations, a deliberate C5 compliance program strengthens security, builds trust, and unlocks market opportunities.