NIST SP 800-171: Protecting Sensitive Data
NIST SP 800-171: Protecting Sensitive Data with key controls, supply chain security, and CUI safeguards to strengthen cybersecurity readiness.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
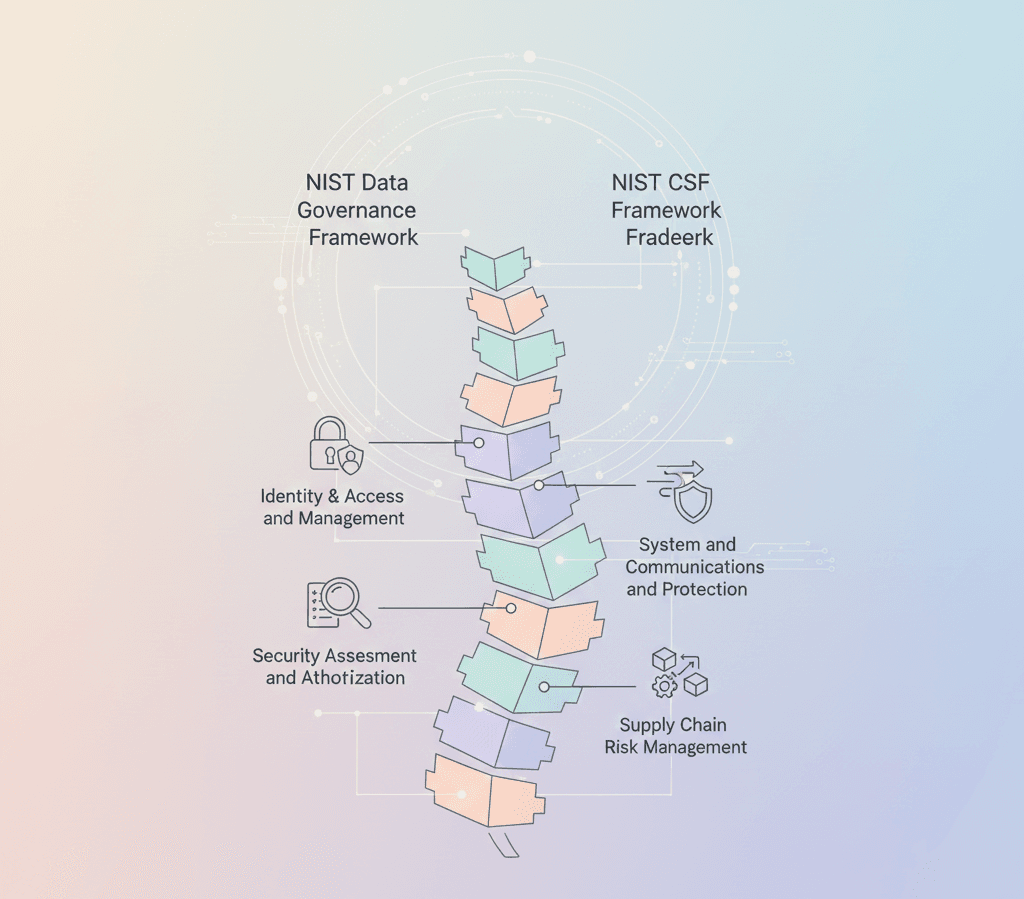
NIST SP 800-171 provides essential guidelines to protect Controlled Unclassified Information (CUI) in non-federal systems and organisations. It plays a crucial role not only for contractors and vendors working with the U.S. Federal Government but also for any organisation looking to strengthen its cybersecurity posture. It aligns with broader frameworks such as the NIST governance framework and is increasingly important in today’s interconnected digital ecosystem, where NIST supply chain cybersecurity and data resilience are critical.
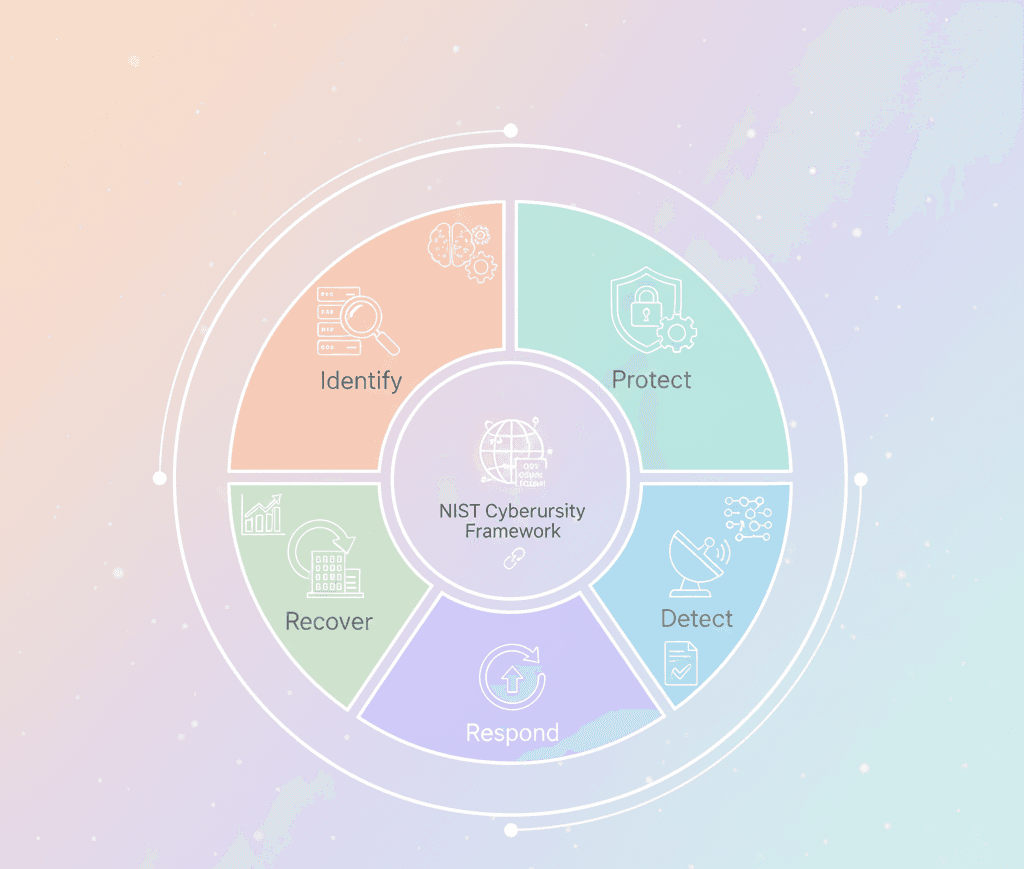
The standard is designed to ensure the confidentiality, integrity, and availability of sensitive information while supporting compliance with other cybersecurity requirements like CMMC and the NIST CSF framework.
Key Elements of SP 800-171
Here’s a closer look at key elements central to the NIST data protection approach, which also integrates well with NIST supply chain risk management and cybersecurity governance frameworks like NIST CSF and SP 800-53:
Access Control – Restricting information access to authorised users only.
Incident Response – Preparing for and responding efficiently to cybersecurity incidents.
System Integrity – Protecting systems against tampering or unauthorised changes.
Audit and Accountability – Maintaining logs of user and system activity to enable accountability.
Configuration Management – Ensuring secure and consistent configuration of systems and devices.
These controls also help organisations align with the NIST supply chain framework and manage vendor-related security risks as outlined in NIST 800 53 supply chain risk management.
Why It Matters
Adopting SP 800-171 helps organisations:
Safeguard sensitive government-related information as part of a NIST data governance framework.
Lay the technical foundation for CMMC compliance, which is essential for federal contractors in today’s NIST CSF supply chain environment.
Establish standardised, repeatable security practices that reduce cybersecurity risk and improve readiness across the entire cybersecurity governance framework.
Organisations that implement these controls are better equipped to ensure secure workflows, protect data integrity, and respond to emerging threats—especially in large, multi-vendor ecosystems involving NIST supply chain risk management.
Conclusion
SP 800-171 is more than just a regulatory requirement—it’s a practical roadmap for protecting sensitive data in today’s high-risk digital climate. When paired with complementary frameworks like the NIST CSF framework and supply chain-focused standards, it empowers organisations to build both compliance readiness and robust, resilient cybersecurity defences.