Red Teaming Demystified: A Deep Dive into Offensive Security
Strengthen your cyber defense with red team testing—real-world attack simulations that uncover hidden risks and improve incident response and compliance.
Accorp Compliance Team
Our team of compliance experts specializes in PCI DSS, SOC 2, and other security frameworks to help businesses achieve and maintain compliance.
Cyberattacks are no longer a matter of “if” but “when.” With threat actors constantly evolving their tactics, companies can no longer rely solely on basic security measures or traditional scans. For organizations committed to building a resilient cybersecurity posture, red team testing offers a powerful, real-world evaluation method.
In this guide, we’ll explore what a red team is, how red team cyber security differs from red penetration testing, and why these simulated attacks are essential for proactive threat defense.
What Is Red Teaming?
Red teaming is a full-scope simulated cyberattack performed by ethical hackers who mimic real-world adversaries. These exercises aim to identify hidden vulnerabilities not just in technology but across people, processes, and operations.
Unlike standard vulnerability assessments, red team testing evaluates your security holistically—testing how well your organization detects, responds to, and recovers from sophisticated cyber threats.
When Should You Consider Red Team Cyber Security?
Red teaming is particularly useful for organizations that:
Manage high-value or sensitive data
Operate in regulated industries (finance, healthcare, government)
Want to test security response beyond basic controls
Aim to meet or exceed compliance with standards like FedRAMP, ISO 27001, or NIST
If you’ve already implemented traditional security measures and want a deeper analysis of your defenses, red penetration testing is your next logical step.
The Red Team Testing Process: Step-by-Step
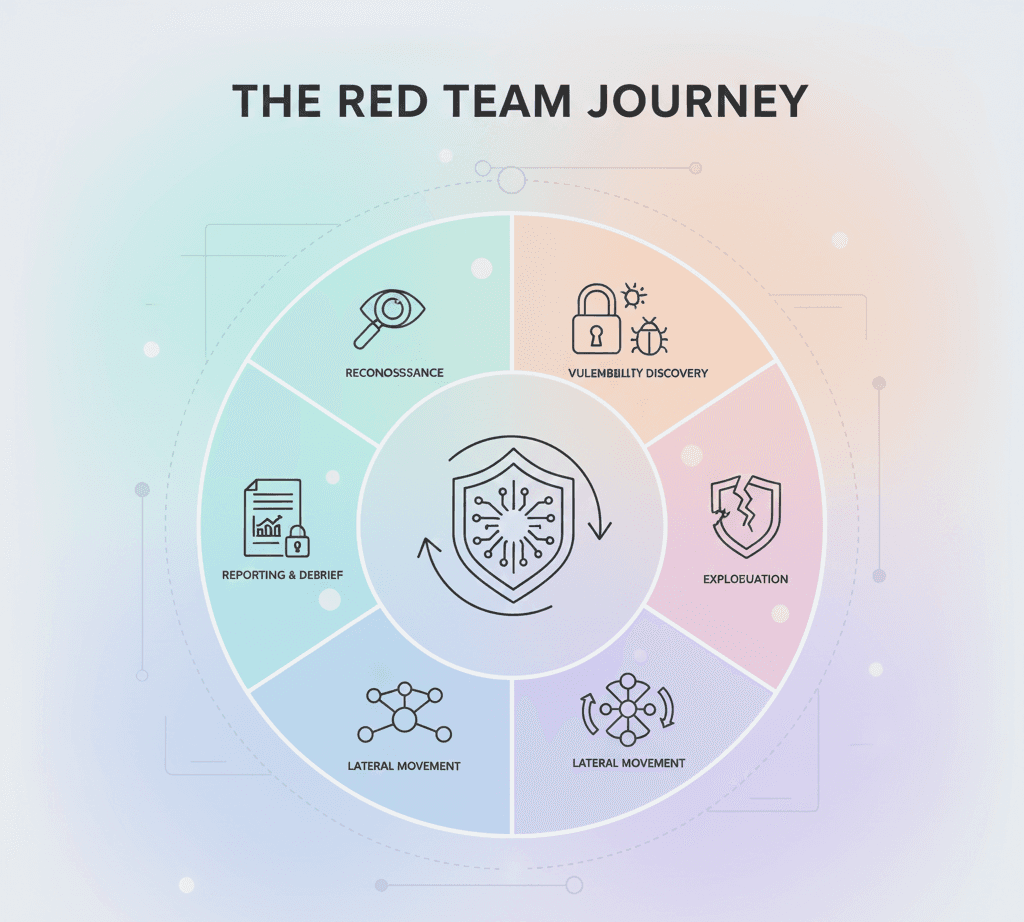
A typical red team testing exercise follows a structured approach designed to replicate real adversarial behaviour. Here's how it works:
Define Scope and Objectives
Establish clear goals and boundaries. Decide which systems, teams, or operations will be part of the engagement.Planning and Strategy
The red team develops tactics, techniques, and procedures (TTPs) that align with real-world attack methods and stay within the agreed scope.Reconnaissance and Exploitation
Attackers begin by gathering intelligence, identifying weak points, and launching controlled attacks—just like real threat actors.Lateral Movement and Persistence
Once access is gained, the red team will attempt to move deeper into the network, maintain access, and reach mission-critical assets, mimicking advanced persistent threats (APTs).Documentation and Reporting
A detailed report highlights exploited vulnerabilities, attack paths, and recommendations for remediation and prevention.Debrief and Strategic Improvement
After the test, teams meet to review findings, discuss security improvements, and define mitigation plans.
Red Team vs. Red Penetration Testing: What’s the Difference?
Many confuse red penetration testing with red teaming—but they are not the same:
Red penetration testing focuses on specific systems or applications, typically with a known scope and objective.
Red team testing takes a broader, scenario-based approach to simulate real-world adversaries across the entire organisation, including physical, social engineering, and network-based vectors.
Think of penetration testing as a focused check-up, while red team cybersecurity is a full health audit.
Benefits of Red Team Cyber Security Exercises
Investing in red team testing delivers far more than just a security report:
Proactive Risk Detection - Reveal vulnerabilities before attackers do, including gaps that traditional assessments may miss.
Enhanced Incident Response - Train your blue team (defensive security) in live attack scenarios. Improve detection, containment, and response under real pressure.
Compliance Readiness - Red teaming helps demonstrate alignment with regulatory frameworks like FedRAMP, ISO 27001, and NIST 800-53.
Holistic Security Evaluation - Test your full security posture—technology, processes, and people—against adversarial simulations.
Red Teaming Is the Future of Cyber Resilience
Modern cyber defence demands more than periodic scans or checkbox compliance. Red team testing allows organisations to challenge their assumptions, expose blind spots, and enhance decision-making under cyber pressure.
Whether you're preparing for a compliance audit or simply want to outpace cyber threats, red team cybersecurity is a strategic investment in long-term defence.
Ready to Test Your Security Like a Hacker Would?
At Accorp, our certified red team professionals bring years of field-tested expertise in offensive security. With a proven track record of successful, regulator-approved engagements, we ensure your red penetration testing and red team testing exercises are effective, compliant, and insightful.